Selling the Digital Transformation Journey: Security & Compliance
When I talk to customers about their Digital Transformation Journey, I always like to give them the “10,000 foot view” so to speak. I suggest that we explore two different angles or “big pictures” in order to paint an image that customers can then imagine themselves into. The first picture is Security & Compliance, and the second is Productivity & The Modern Workplace. Let’s start by examining the first.
With regard to Security & Compliance, we have to set the stage a bit: why should customers care about this stuff? After all, cybersecurity initiatives typically struggle to get funding and other traction, especially in the small and mid-sized business where resources are more scarce to begin with.
The structure of your pitch
You will often see security vendors at conferences begin their presentations with scary statistics about how many breaches occur each year, and how the cost of an average breach has been steadily increasing year-over-year; I find this type of information to have a very limited effect on people. If something like that is going to be your angle, it is far more effective to relate real-life stories, and the “closer to home” each story hits, the better (yet some orgs will refuse to act until it is their own home which is hit, and they become one of those stories you end up telling to others).
But selling customers on the importance of security & compliance should not be based on scare tactics, anyway. You also have to paint a picture of value. Give them a preview of what it looks like to live in the new world you want to guide them into. Remember that all changes are going to be met with some resistance (this is only natural), yet these changes are ones that must take place sooner or later. Plus, you can highlight new features such as Sensitivity labels, which grant users new superpowers they’ve never had before. In general, it is much more difficult to prod people from behind into the darkness than it is to coax them into the light, leading from the front. In other words, carrots are better than sticks.
The corollary in this message which you must communicate explicitly is that you have already walked this path yourself, and you have no regrets about doing so. You will also take them down this path, and it will go just as smoothly, or even better, since you already know the pitfalls and dangers that lie along the way. As you paint this canvas, also be sure to highlight how the new tools or capabilities would have prevented or mitigated the problems you shared earlier in your anecdotal stories.
In addition to sharing relatable anecdotes and painting the preview or picture I want them to inhabit, I normally make it very clear that this past decade has seen such a radical shift in the cyber landscape, that I can no longer afford to waste my time with customers who will not take this journey seriously. If they cannot even be bothered to implement a basic level of cyber hygiene such as CIS Implementation Group 1, then they are essentially begging to be compromised, and simply I cannot give my precious attention to folks who will not even address the most essential of risks, and therefore any further engagement is off the table. This is also why I suggest beginning your new engagements from Security & Compliance rather than Productivity & The Modern Workplace.
Let me be clear: this might mean you have to fire some existing customers, even long-standing ones. But that’s okay: you are going to replace them with better ones (the ones who will actually listen to you and trust your recommendations). Notice this is different from either a stick or a carrot. It is more like a “filter” or disqualifier. Holding up this barrier is only fair to them, and enormously helpful for you, plus it sends a very strong message (it projects confidence in your own practice).
So let’s review: you should plan your Security & Compliance pitch using these key components:
- Relatable anecdotes from the wild (and the closer to home the better)
- A preview or “picture” of where your customer is heading and the new capabilities you will bring to them
- An ultimatum / disqualifier
So what does good look like?
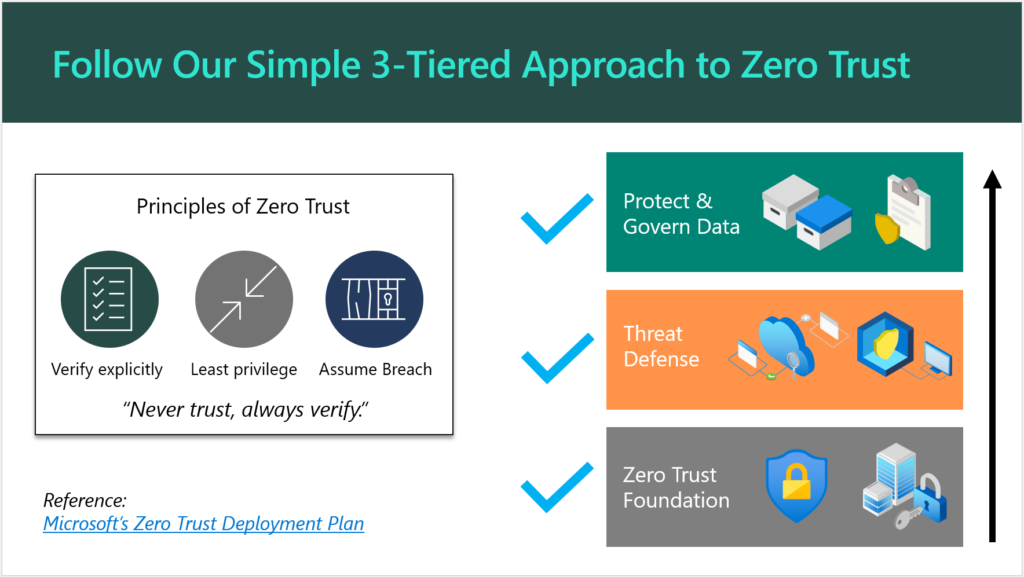
Once you have a prospect’s attention, you will need a simple and engaging way to explain your Security & Compliance offering to them. If you are primarily selling solutions built on top of Microsoft 365, as I am, then I suggest leveraging the concepts, marketing and language that Microsoft themselves have already produced. For example you will see them speak and write frequently about “Zero Trust,” and what that phrase means to them.
They have also published some detailed documentation such as the Zero Trust Deployment Plan, which is targeted for Enterprise (read: E5) customers. You can simplify this for SMB a bit further, as I have done here:
There is no need to reinvent the wheel (that’s what Microsoft’s materials are there for). Plus, if a customer decides to “spot check” your pitch, they would find solid validation with a quick Google search.
Aren’t Security and Compliance different things? Why not two offerings?
You can sell separate offerings if you want to, sure. Remember that a “compliant” environment is not necessarily a secure one. On the other hand, the items that are generally called for in a high-regulation, compliance-intensive scenario most often exist because of concerns around data security. For this reason, I always suggest that you approach your engagements from a “Security-First” mindset. When you build a good, secure foundation, you will very often find that compliance is a breeze thereafter, and this is because most compliance requirements will map back to common cybersecurity frameworks such as NIST anyway.
And yes, I am aware that in some cases “compliance requirements” actually contradict the latest cybersecurity guidance. The most common example I see thrown around is password complexity & rotation requirements, which are moot after the implementation of a good Zero Trust baseline including Multi-Factor Authentication and other identity protection systems. Look, I have gotten into with auditors before: I have found that the spirit behind the law is more important than meeting the letter of the law itself. So with regard to this particular example, the point is not to put people through the discomfort of changing passwords every 90 days, the point is to protect them from credential theft and identity compromise. We have better, more sophisticated ways of doing that now which are more comfortable, so why would we go backwards? I have fought this battle and won on more than one occasion (so that we could end password rotations), and I won because I supported my claims with reputable references.
Anyway, my original point is that you can splinter off a cybersecurity essentials baseline offering, and then have “compliance” add-ons for helping organizations meet more specific requirements such as PCI, HIPAA, GDPR, etc. as needed. Some service providers will specialize around a particular vertical, and get to know their requirements really well, and then just focus on those (then a single, flat-rate Security & Compliance offering makes a lot of sense). How you bundle this stuff and sell it to your customers is largely up to you. I would not say there is just one right answer here.
Conclusion
Once your customer has committed to the Security & Compliance journey, then you are off to a very good relationship indeed. From here, you can begin to explore the next big picture, which is improving productivity and modernizing outdated, tired business practices. This will require a new change of frame, so to speak, and another pitch. But this second journey is going to be taking place against a more secure background than what you had before (this actually makes life easier and less stressful for both you and your customer). Without the first journey, you could jeopardize all of your subsequent efforts in the second: the modern workplace transformation should be undergirded by that Security-first foundation.
If you enjoyed this blog post and would like to see more content like it, which goes into greater detail and gives you an opportunity to work with myself and other peers who are implementing these solutions for customers, I would suggest you check out our SquareOne Practice Development Group.
After you get your customers onboarded to your “Security-First” services, the next step is helping them to complete their digital transformation and maximize the value they invested into the modern workplace. But that is a topic for another day.



Comments (2)
Alex, do you think there is a minimum customer size in terms of users or turnover that we as Microsoft partners should be targeting in the SMB space that would be interested in the Security and Compliance picture? From a MS partner perspective for the SMB to register for us towards a silver partnership it must have at least 10 users… which in regards business premium would mean they must be spending at least £166 on MS licensing per month alone, MS would suggest partners should be looking to make £5 for each £1 customers spend on licensing, which would mean the customer spending £830 per month on their overall ICT provision… which itself suggests a monthly turnover of (say) 10x (based on average turnover % spent on ICT / Digital being around 8%)… which would mean businesses with monthly turnover over £8k.
I do not think there is a minimum, no. That having been said, some MSP’s will not be concerning themselves with MS partnership goals at all in very small numbers. For example, I know of MSPs who do not use CSP or any other model to resell licenses, but rather just encourage their customers to purchase from MS directly. And then they still sell services to manage the security & compliance aspects within the environment. This requires you to know your own market. For example, here in the US, one of my customers specializes in small financial services firms, often less than 10 users, and they are able to charge a decent price per user for their service, and have excellent retention rates with minimal turnover. So it is possible to set up a successful business in this space at any size in my opinion, but it is dependent on you to know your target market, create the value and then get and maintain your customers.