Multi-tenant management for Microsoft 365, and other things
IT service providers are constantly looking for more efficiency, and better ways to manage their customers’ hardware and software assets. In the Microsoft realm, we finally have Microsoft 365 Lighthouse, which is now in public preview. Some of my MSP customers have raised question marks around its current feature set and long-term development. I think it is off to a great start, and personally I am very optimistic about the future of this product. But that doesn’t mean that it will meet all of your needs on day 1.
What it will do is give you a centralized view across customer tenants, users, and devices, as well as some shortcuts to several common tasks such as resetting a user’s password or reviewing threat information from Microsoft Defender and executing antivirus scans on devices. Then there is Baselines, which are standard templates for controlling critical security policies such as MFA, device enrollment, and device compliance.
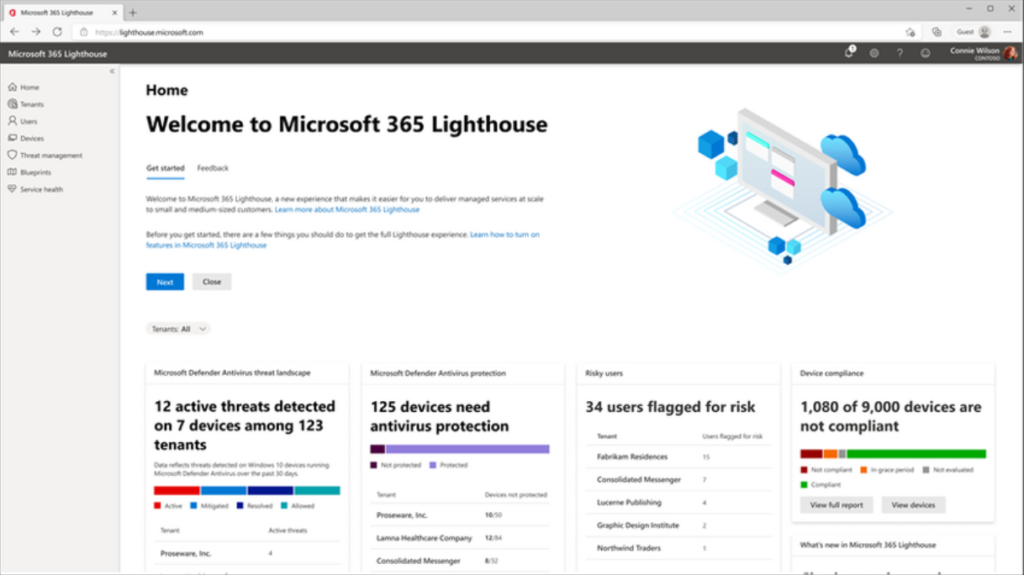
Like I said, it is a really good start in my opinion, but partners often want more.
Patience! But also, did you know?
The truth is that today, we rely on several different tools and portals to get our jobs done, and I think that is probably nothing new for most MSP’s. Remember when we thought our PSA, or RMM would be the tool that solved all our problems? I don’t know that we can ever get down to just one pane of glass. But what can we do right now, beyond just the Lighthouse tool? Here are I want to go over a few considerations for Microsoft partners that can be important depending on what all you are including in your services agreements. That is, what have you actually agreed to monitor and support? This also helps to illustrate some of the opportunities if you aren’t already aware of them.
Alerts from the Security Center
When you on-board new tenants you absolutely must enable the Unified audit log and the default Alert policies in the Security/Compliance Center(s). I also recommend installing a few custom alert policies to monitor for potential Azure AD incidents, such as app consent abuse.
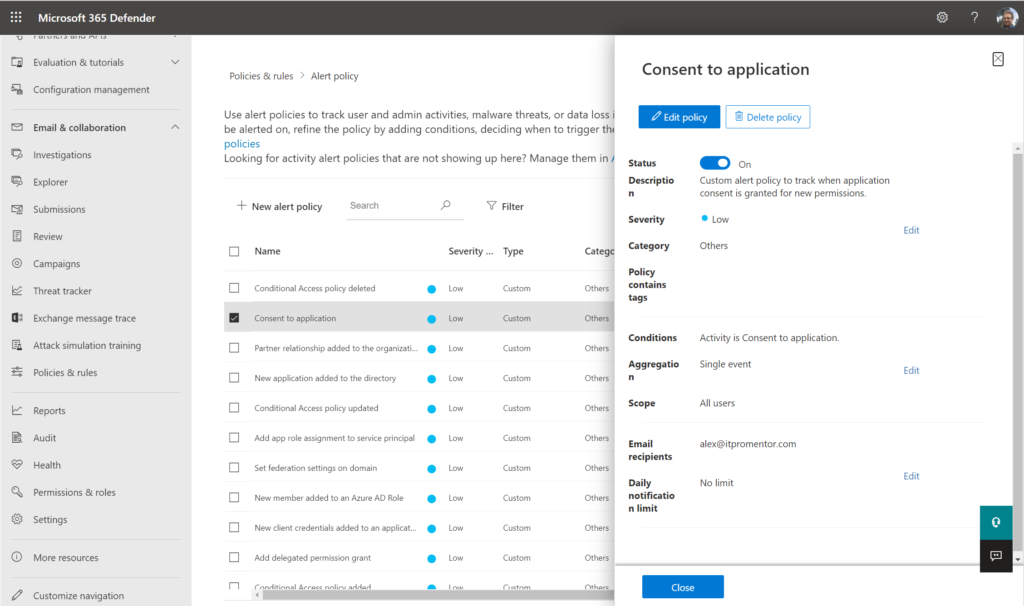
Alerts can be configured to send email to an external address such as “[email protected]” or similar. So far these alert policies are not visible/accessible in Microsoft 365 Lighthouse, so you have to get into each tenant individually; make it part of your on-boarding checklist! It is also not a bad idea to audit this quarterly or at least semi-annually with a “tenant maintenance visit.”
Side-note: There may be third-party tools out there that help you monitor these things. But I hope to see them added to Lighthouse someday!
Microsoft Cloud App Security
If you are managing customers with E5 or the MCAS add-on, then you have additional alerts, and those email notifications must also be configured separately. The neat thing about these more “advanced” alerts is that you can customize the “from” address so that it appears to come from your customer’s domain. This is helpful for MSP’s who want to use their ticketing system to automatically associate the ticket to the correct organization.
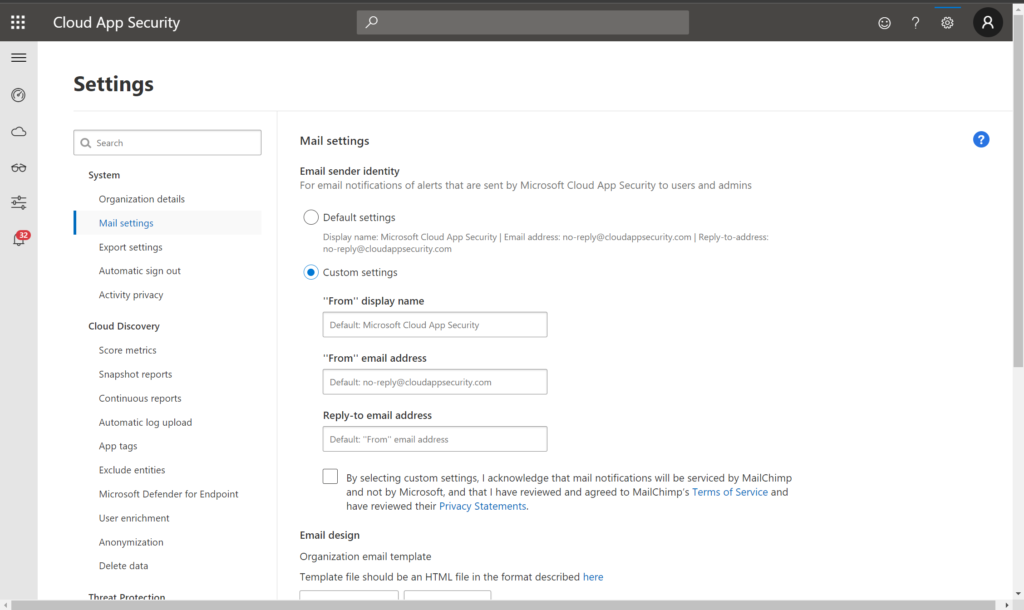
Keep in mind that E5 customers can actually include all the alerts from Microsoft Defender for Identity (which provides monitoring for on-prem AD incidents) using this tool as well.
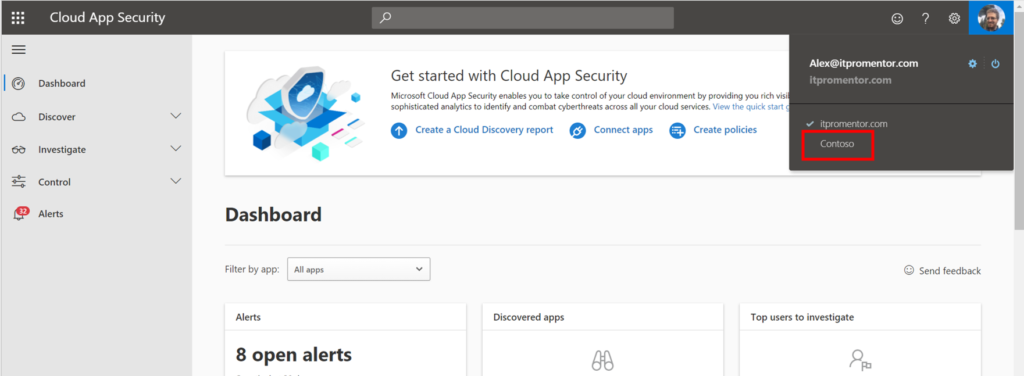
Another important item to highlight is that each customer’s MCAS portal can individually be set up for external admin access; it is a very easy process of adding external email addresses from the partner organization and assigning the appropriate role, and it is completely separate from your other Partner relationships/delegated portal access.
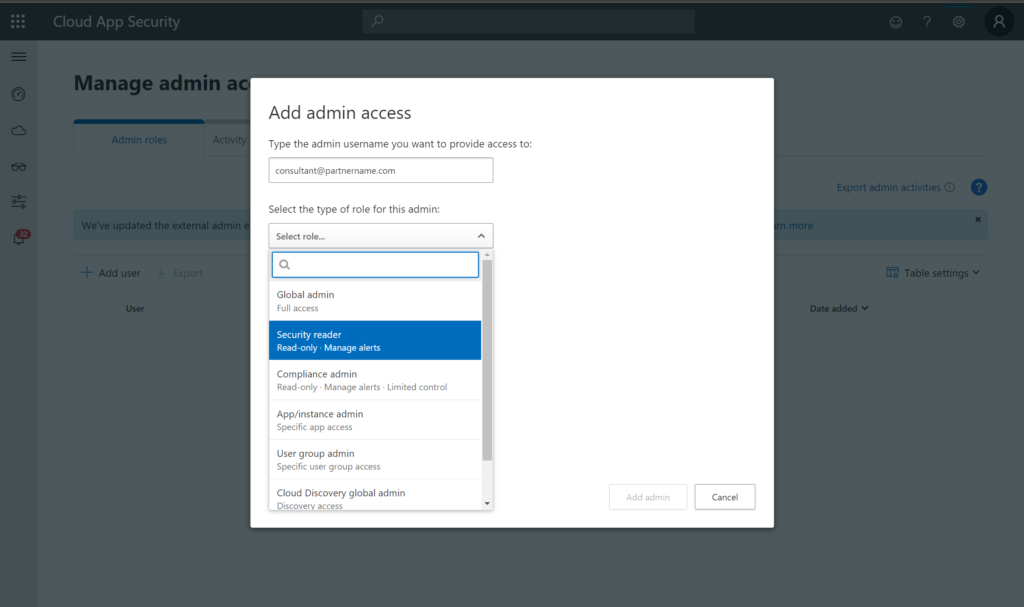
Switching tenants is a breeze from the partner tenant at portal.cloudappsecurity.com.
Microsoft Defender for Endpoint
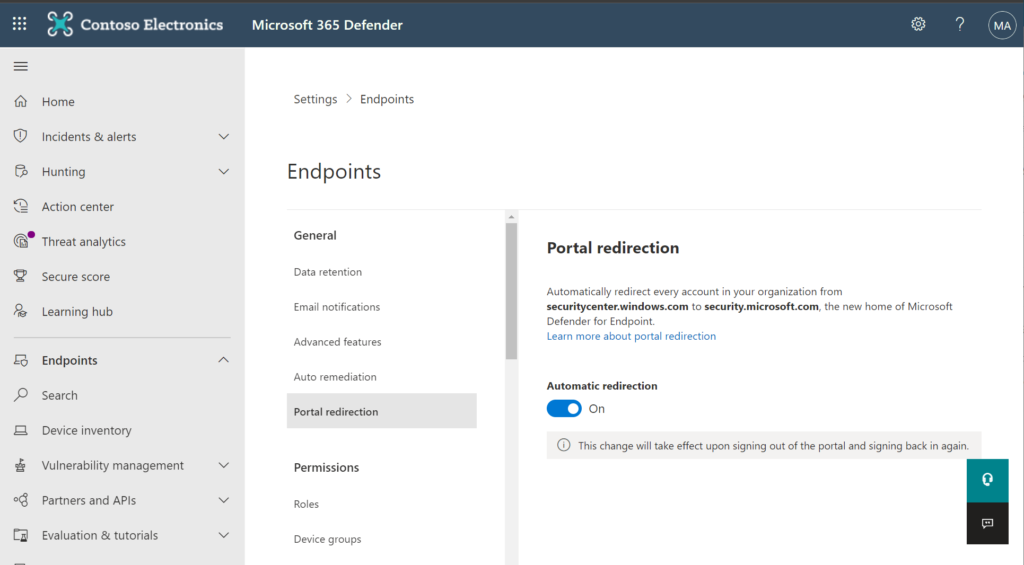
As of today, Lighthouse covers some of the Next-Gen Antivirus features of Microsoft Defender, but it doesn’t include the more advanced stuff like EDR or ASR, which we get with Microsoft Defender for Endpoint (MDE) P2, included with M365 E5. To manage these items you need to sign into the individual tenants also, and use the new Security Center. It is now possible to manage all MDE features right from the Security Center, by enabling the portal redirection feature under Settings > Endpoints.
You can also configure notifications for Microsoft 365 Defender services, and again we have the option to set up delegated portal access for outside partners. This process is a bit more involved than what we had to do for MCAS, so be prepared for a bit more work to get that all set up.
At the end of the day, it still requires you to switch tenants and view customer instances one at a time, so it is not as ideal as something like Microsoft 365 Lighthouse, but that’s where things are at as of today.
Azure Sentinel + Azure Lighthouse
Since we are now up to several portals, and we may have other assets to monitor besides (e.g. on-prem devices), another option is to configure Azure Sentinel, Microsoft’s SIEM/SOAR product. Here we can ingest events from all the Microsoft 365 services including Azure AD, Office 365, and all the Microsoft 365 Defender products such as MCAS, MDE, etc.
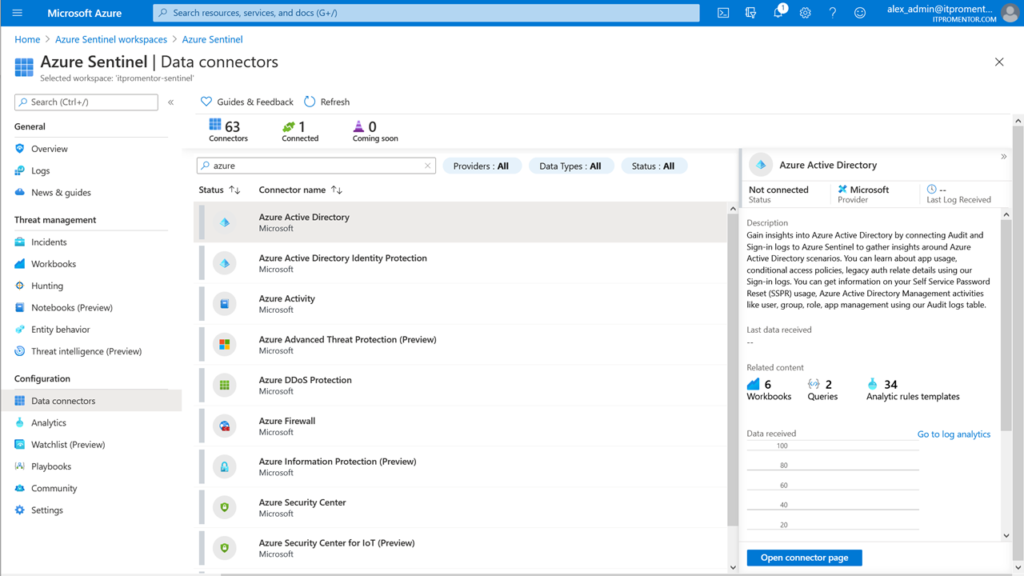
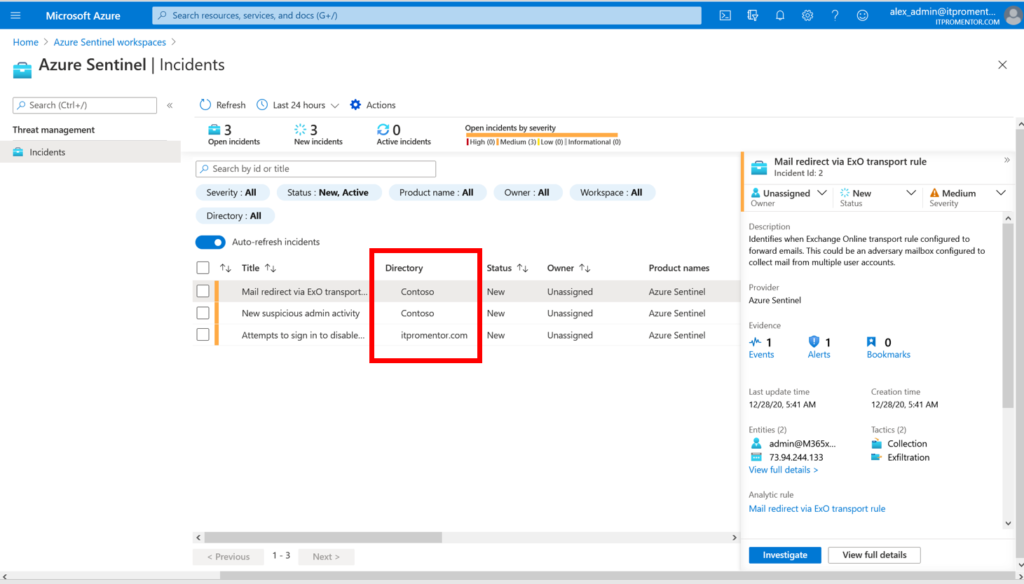
The real benefit of course is that once you have Sentinel configured, you can also layer on Azure Lighthouse, which is the counterpart to Microsoft 365 Lighthouse on the Azure services side of things. Now you can have multi-tenant views of incidents across your customers and more easily switch between the Sentinel instances that you manage.
Not just one solution, yet
So the lesson is, you probably aren’t just relying on a single solution right now, especially if you are managing more of the advanced services under E5 licensing. I am excited to see what the future holds as Microsoft 365 Lighthouse is still so new! There is a lot of potential here, but the two Lighthouse solutions (Microsoft 365 and Azure) look to me to be the future. The ability to switch portals and so on isn’t all that appealing, but we do it begrudgingly until something better is available. I guess it all comes back to that patience thing again.



Comment (1)
We use Simeon Cloud for this