Migration paths to Microsoft 365: Devices before data??
I have literally written the book on this topic, but one question I did not directly address is the order in which you might migrate the various workloads from traditional infrastructure to Microsoft 365.

First, just know that you can tackle your migration in whatever order works best for you, but there is a specific order that I recommend, and I will be transparent about the reasons I recommend it so you can decide for yourself how you want to approach your own project.
Note: This is about moving to Microsoft 365, not just Office 365. See here to learn why you need a modern management and security framework for a cloud-first, mobile-first world.
Hybrid Azure AD environments

I believe hybrid will still be the most prevalent architecture, at least for the next 2-4 years. Smaller orgs with no or very few LOB apps on-prem will be able to leap off even sooner than that (and some indeed have), but for the majority, hybrid is going to be the destination for now. Cloud-only will come eventually. But for hybrid customers, this would be the path I recommend:
- Identity + Email (many orgs have already done this)
- Windows 10 + Endpoint management (including hybrid join)
- File sharing + Collaboration
And, I argue, you should be addressing governance, security & compliance at each stage of the process.
Identity + Email
Identity + Email is where almost all organizations who moved to Office 365 started, and that trend will continue to remain true as time moves forward. The reason is simple. Email is a commodity and a very low cost of entry from an effort perspective for immediate benefits. The migration of this workload is also considered a commodity now; it is perhaps the most well understood migration “in the trenches” today.
It is also worth noting that having your mailboxes in the cloud is a pre-req for certain other items that come later on. For example, copies of chats from Teams are saved to your cloud mailbox for compliance purposes. And there are other benefits to having your mailbox in the cloud before you get into file sharing and other apps.
But before going any further here, I would add that you absolutely must implement Multi-factor Authentication at this stage if you haven’t already. Just get it done–and I don’t mean to suggest that MFA is a “cure-all” by any means, but it is a major win for security, and it is no longer optional (it’s also just not that hard these days).
Windows 10 + Endpoint management
Now in my perfect world, I would argue for addressing endpoint management as soon as possible, right up there with identity, and even ahead of mailbox migrations if I could. But the reality is that many have already completed the first move without doing much about devices at all. So here we are.
Unfortunately too few consultants and IT providers out there are aware of the importance that devices play in the overall strategy, and the impact that a properly thought out device and application management policy can have. Yes I am talking about Windows 10–but I’m also addressing every other device that participates in corporate apps & data! Why? Because devices are another important leverage point you have in deciding how to govern and secure access when you’re hosted on a public cloud.
At a bare minimum, I would suggest that you deploy application protection policies to encrypt corporate data on devices whether they are being managed or not. This gives you a kill switch–to wipe that data remotely as needed. Think departures, terminations, loss, theft–anywhere you would not want corporate data left exposed to the wrong person(s). You can do this without impacting personal data, so it’s great for BYOD scenarios (very common in the SMB).

Next: you need to decide under what circumstances you would allow full access to corporate data, and whether you might benefit from restricting access–to at least some of that data–based on whether the end user is working in a corporate context, on a managed device.

Implemented correctly, the cloud will be able to recognize the difference between a corporate and non-corporate device no matter where it is in the world. And that means you have powerful leverage when you’re creating Conditional Access security policies to protect sensitive data in places like SharePoint and Teams.
For example, you can limit or even block access from non-managed devices under specific circumstances. You can do it wholesale, or coming soon, Sensitivity labels can be used to provide this protection at a more granular level for individual sites and groups (e.g. Teams). Admins can also turn this on per-site in PowerShell already today. But again this kind of thing is possible only when the cloud can understand the difference between corporate and non-corporate endpoints.

Now, for hybrid organizations, establishing a more modern approach to managing devices isn’t that difficult–it means going through a quick and painless process using Azure AD Connect and a GPO or two. Side note: Hello for Business requires a bit of additional set up, if you plan to support that in your org (and you should)!
What if I’ve already proceeded to files and collaboration with Teams, OneDrive, etc.?
If you moved forward with bringing files to the cloud ahead of devices, don’t sweat it–you can still do devices after the fact and add these protections on later, but if you are just getting going with your migration, why not do it right and establish these boundary lines from the start? Just make better security part of the experience from Day 1! Therefore, I generally place devices ahead of files. But again–not 100% necessary–just my preference.
Teams is perhaps the hottest application in the ecosystem right now–the one that everyone is eager to adopt, and many out there jumped on the bandwagon quickly in their efforts to “transform.” But, they are learning that Teams isn’t as easy as they thought it would be, and so I believe we’re starting to see the marketplace slow down, mature a little bit, and approach these things with more thoughtfulness, as well as some healthy skepticism. That’s not a bad thing–it will help organizations take their digital transformation initiatives a little more seriously (it’s not just about throwing some new tools at people).
So if you get a little bit of breathing room between Exchange and these other workloads, I suggest you take a real hard look at the state of your devices. Note that you should be up to date with Windows 10 in order to support the best features in OneDrive for Business, such as Files On-Demand. Oh, and if you don’t already have the latest Office bits for the desktop installed, do that now as well. These pre-reqs will make for the best possible experience when you start working with the productivity suite and file sharing experiences in the cloud.
Files + Collaboration
File servers: the next step in the typical “exodus” from on-premises systems. There is more to this process than meets the eye. I have written extensively about this topic, since it is going to be more involved than your Email migration (which was just sliding mailboxes over all at once). Can’t do that with files, nor do you want to. And of course, I have an opinion on the “best order” for file server migrations as well.
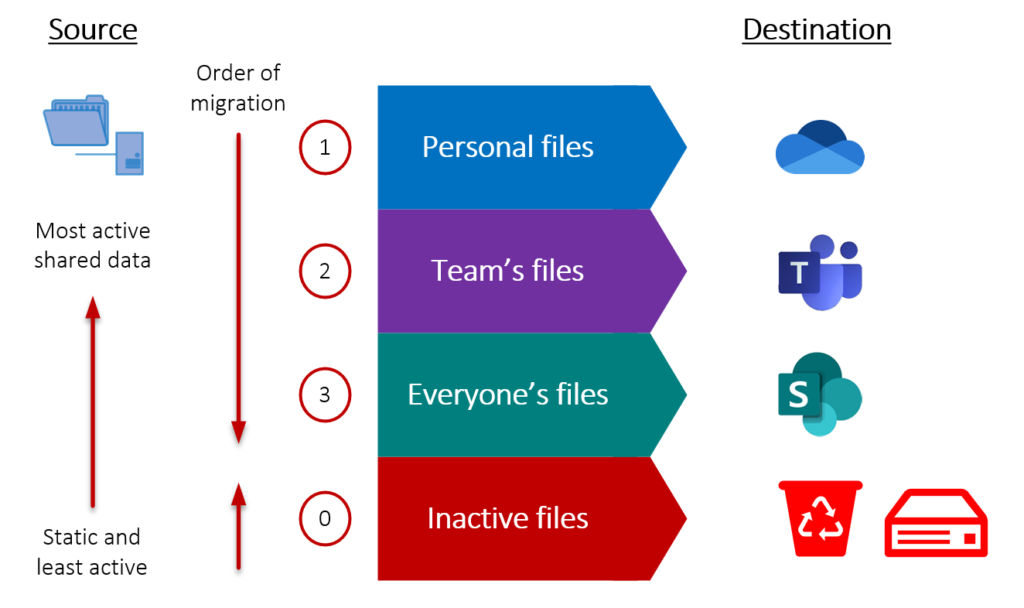
In short, it is a slower, user-driven process (not a cut-over orchestrated by IT). Reasons being: destination cloud locations are not 1-1 with on-prem source locations, and nobody knows the data better than end users–they are going to know what to bring, what to get rid of, and what to put where. Because of the additional complexity of adopting the modern information system and moving data into the right places, file migrations tend to come after the other pieces such as email, which are easy to transition with minimal impact.
But it is worth noting that, even though it is harder to move through this transition, you get more benefit in the end. It’s not just relocating files from one container to another–it is about upgrading your capabilities and taking work content out of your day.
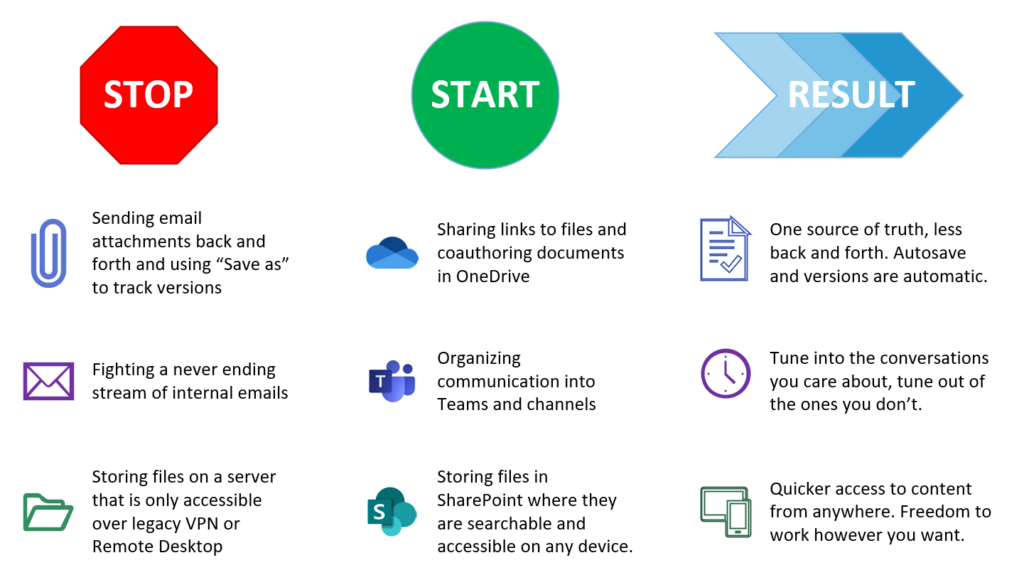
When it comes to security and compliance, you will want to take a close look at your options for data protection as you start working with your files in the cloud, including data classification e.g. retention and sensitivity labeling. Your data classification and labeling, retention, and other compliance requirements are an important piece to review when you undertake the move to modern cloud-based collaboration.
Keep going!
Please note that this is only the beginning of the digital transformation journey, and that “beginning” culminates in an adoption of modern file sharing and collaboration tools like OneDrive, Teams, and SharePoint Online. However, after these goals are accomplished it is likely that organizations will want to keep on pushing forward, to get even more value out of their investment in Microsoft 365–it is after all “The World’s Productivity Cloud.”

Thus, Line of Business applications will most likely be the last thing to be “transformed.” No platform out there is better positioned to help you enhance or even displace legacy LOB apps than Microsoft 365 with Power Apps, Power Automate and Power BI. While you could start using these tools even now, ahead of any migrations, the value of the Power suite of apps increases as you put more of your communication, files and collaboration into Microsoft 365, so that those tools and repositories can be leveraged when you are creating your own custom no-code/low-code apps and workflow processes.
Whether you are keeping your legacy third-party LOB apps, or migrating to more modern SaaS alternatives, it is likely that you will be able to attach to those apps and build more value using the Power platform. I suspect most organizations will be starting with the basics and moving on up from there, but don’t feel like you have to wait to begin exploring the possibilities just because of the graphic above.
Ready for cloud-only?
If you are aiming for “cloud-only” and your intention is to shut off any legacy on-prem servers, the only difference is that you will perform full Azure AD join for computers, rather than hybrid join. This requires that you disjoin existing computers from the local domain and rejoin them to Azure AD, giving each user a new profile (no, do not attempt to migrate the user profiles).
In my experience, the best place to start is hybrid join, until you are ready to kill your old server for good, then transition the remaining PC’s to cloud only. However, users who are always out of the office, like a mobile sales team, can probably transition to cloud-only at any time. Just be mindful of the users who require regular access to local network resources that are still hosted on-premises.
While you could transition computers to cloud-only first, you would need to manually map stuff like shared printers* and files from the old server until you were ready to cut the cord on that stuff, or write a custom script and push it via Intune to do the same. But hybrid is the least disruptive (users don’t really notice that you implemented it–no need for new profiles, etc.).
*Aside: There really isn’t a good “built-in” solution to cloud-based printer sharing in Microsoft 365 (yet–but Universal Print is coming soon)–in the meantime, check out Printix, which is a cool third-party tool that integrates with Azure AD and Microsoft Endpoint Manager / Intune nicely. I have no affiliation with this company.
Conclusion
And that’s really all there is to it. Yes, Microsoft 365 (and other cloud apps) can completely replace your legacy on-premises servers. But very often hybrid is the reality at least in the near term. Either way, the migration path is clear, and along the way we actually pick up superior security & compliance features to support a cloud-first, mobile-first workplace.



Comments (4)
“There really isn’t a good “built-in” solution to cloud-based printer sharing in Microsoft 365 (yet–but Universal Print is coming soon)”
Hopefully this comes to Microsoft 365 Business. The MS article says Windows 10 Enterprise or Education is required.
Thanks Alex for another gtreat article.
This is really good..
Thank you for a useful article.
Where do you fit migration to the online Office Suite in this sequence?
There is no migration necessary for “Online” apps–if you mean the ones that you interact with in the web browser. If you are working in OneDrive, SharePoint Online, then by default clicking on a file opens it in the online web apps. As for upgrading the desktop apps, the very easiest way to do that is to deploy the apps using Intune, in other words, just one more reason to do devices first!