How to configure Mobile Application Management (MAM) with Microsoft 365 Business (and Intune)
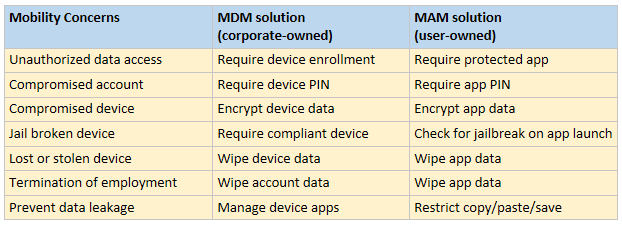
With a traditional MDM solution, the goal is typically to impose management controls at the device level–enforcing policies like pass code with automatic screen lock, encryption, and remote device wipe. It can also be helpful in tracking inventory of mobile devices. All of these “MDM” features are important, especially when the end points are corporately owned.
But the vast majority of small businesses do not provide corporate-owned and managed mobile device hardware to their employees. Most often, the SMB employee is “bringing their own device” (BYOD), and using corporate email and other applications alongside personal apps and data.
Enter Mobile Application Management (MAM). This is a solution available with Microsoft Intune subscriptions, included with Microsoft 365 Business and Enterprise plans, or via the Enterprise Mobility + Security suites. MAM allows administrators to exercise similar controls at the application level, instead of managing the devices themselves, which is ideal for a BYOD situation.
Today I am going to demonstrate how to configure MAM using a Microsoft 365 Business subscription. Later, in a follow-up post, I will add Azure AD Premium into the mix (sold separately from Microsoft 365 Business). Using Conditional Access, we can steer users toward the corporate approved apps, and enforce other rules which can raise our confidence level in the access requests coming from unmanaged devices.
A quick bit of history–when Microsoft 365 Business first came out, the full version of Intune was NOT part of the subscription, but this MAM functionality was still exposed via the 365 Admin center. However, full Intune capability is now available with the subscription bundle, so MDM policies will also be possible for you (hoping to see more easy-to-use policies added when the recently announced admin center updates are complete). I’ll keep an eye on this and post updates as this develops.
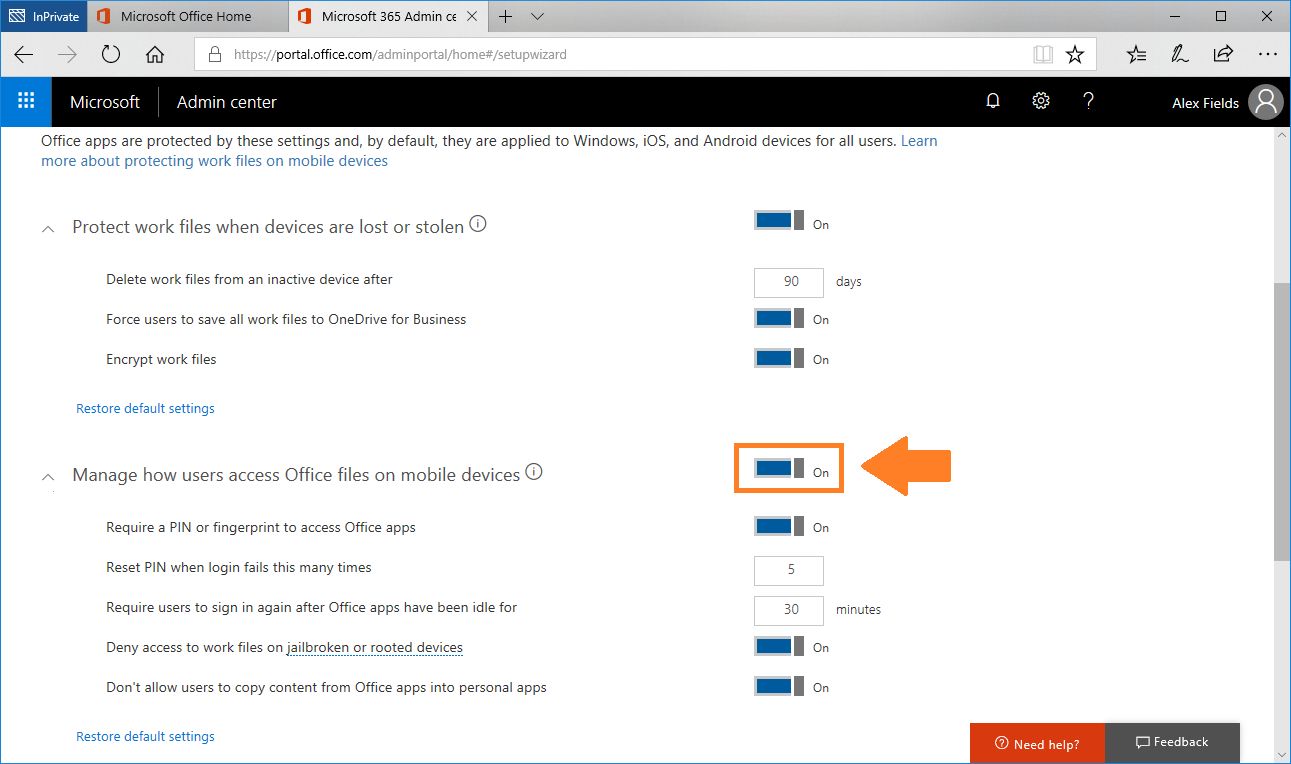
When you first setup the subscription you will have the opportunity to turn these policies on:
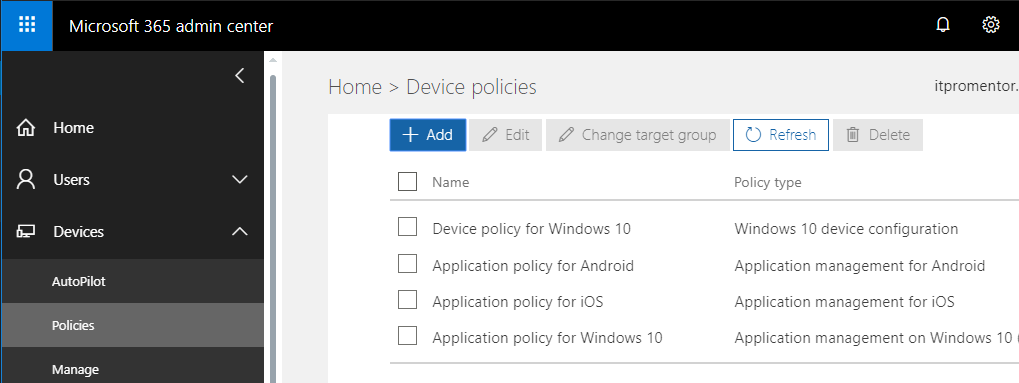
And then later, you will find them accessible also through the Microsoft 365 Admin center. Note: we are expecting some updates to the Admin Center soon, so these screens could look a little different by the time you read this, in the future. But right now you can find it located under Devices > Policies.
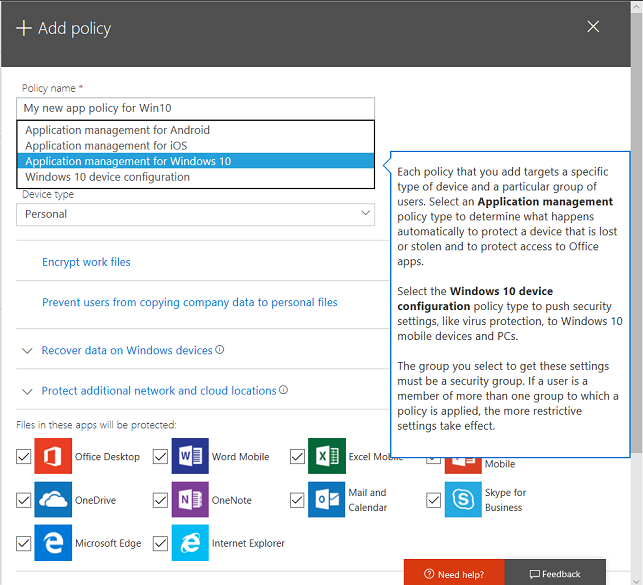
If you try to Add a new policy, at this time, we have the option for Application management policies (MAM) on Windows 10, Android and iOS. But you only have device configuration policies for Windows 10. Now that the full version of Intune is available as part of the Microsoft 365 Business subscription, I hope that we will see additional device-level management (MDM) options added here. *Fingers crossed*
Update: You should NOT use the Windows 10 application policies from this wizard. If you decide to use them, configure via Intune instead. You have been warned. I have not found any issues with the iOS/Android policies.
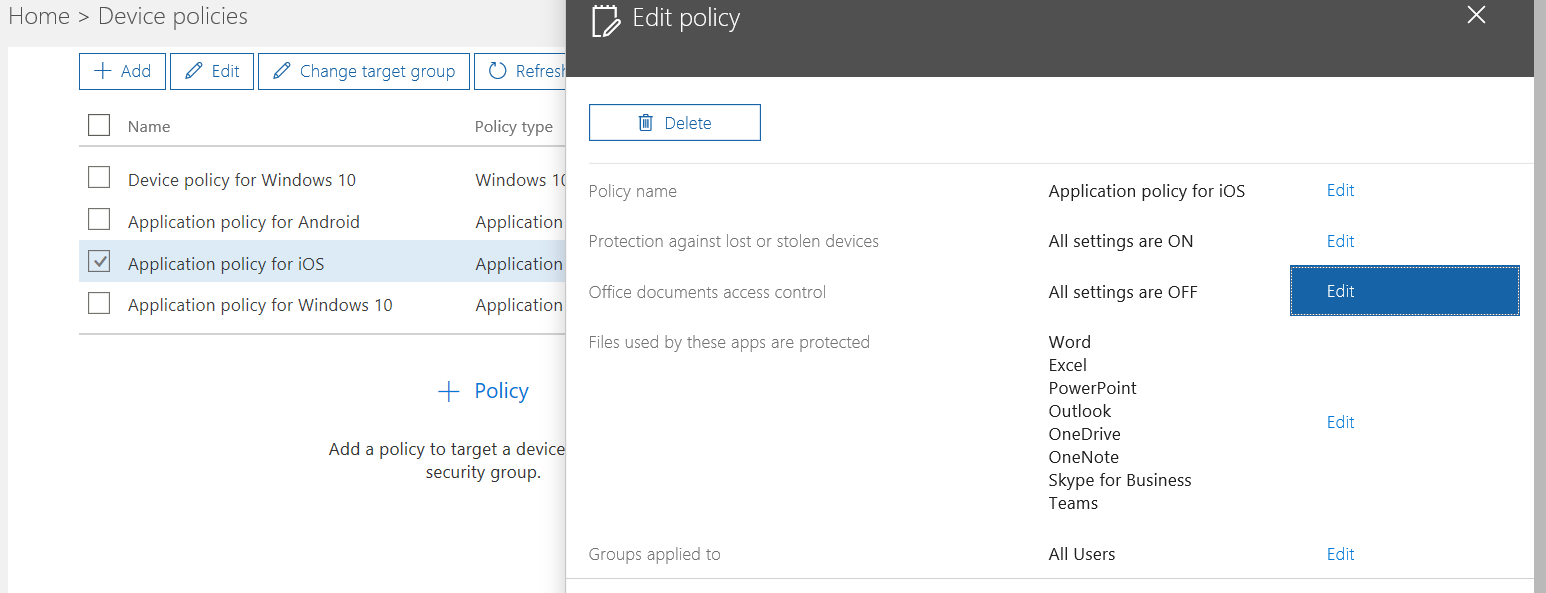
You can also Edit one of the existing policies to see what options you had selected during the initial setup, and so that you can change your mind and tweak them down the road.
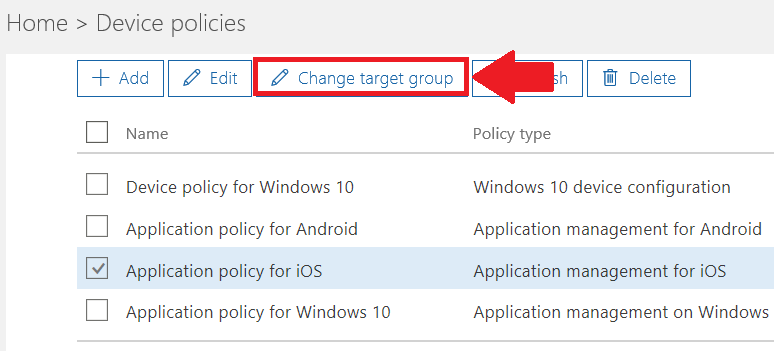
Note that you can furthermore apply these policies, targeted to specific groups of users (by default they apply to all users). So you can have more or less restrictive policies. Just know that if two policies conflict, and a user falls under the scope of both of them, the more restrictive setting will always win.
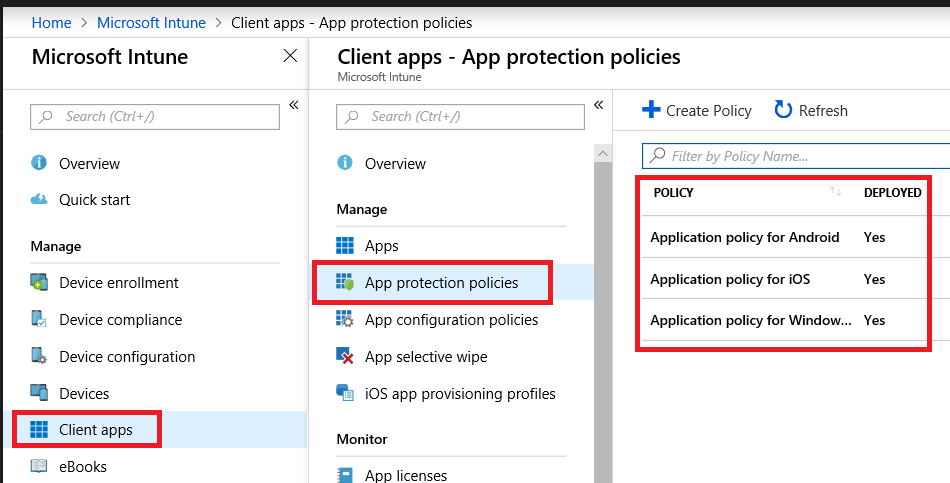
View the policies in Intune
To see what this looks like under the hood, hop over to Microsoft Intune from the Admin centers area, and find Client apps > App protection policies. They should all show up in here.
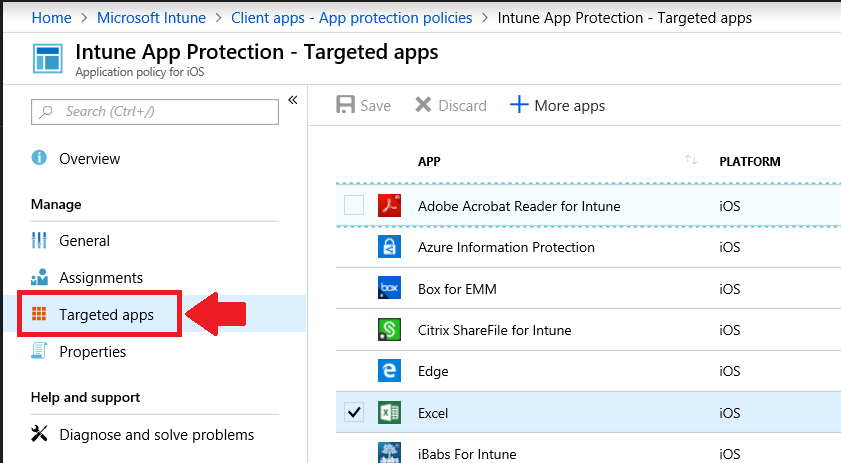
Selecting one of them, you can browse the various settings and options–you will notice it is possible to manage additional apps, also. Choose Targeted apps.
Under Properties, you may even find a few other settings to expose, which are not available via the 365 admin center (yet).
Another time, as I mentioned above, we will look at how to layer Azure AD Premium on top of this setup (sold separately from Microsoft 365 Business), to enable Conditional Access–after all, when you aren’t managing devices, you may want other ways of “raising your confidence” in the access requests made against the application.


Comments (13)
Thank you for this as it is becoming clear to me in terms of how MAM can manage BYODs. One cloudy area for me, does the user for example on an iOS device, do they need to add the company portal app or just download the apps that will be managed? Regards
For iOS, you will want the Outlook app (and any other managed apps such as OneDrive, if those are desired), and you will also want the authentication app, which is used to register the app in Intune. For Android, the registration process leverages the Company Portal app. I’d like to see the two experiences converge but for now that’s what we got.
Hi Alex,
Im coming across some documentation that mentions “App configuration policies”. It seems to say that you ought to set an app configuration policy up for each app that you configure an app protection policy for. Is this correct? what do these policies do?
Thanks
Until very recently you could only apply App configuration policies to managed devices, but now you can also apply them to unmanaged devices (without enrollment). Yes, they can be handy depending on what you want to do. Allows you to configure options in the app, for example in Outlook I could turn on the “Save contacts” feature. Stuff like that. On a managed device, you could even auto-magically sign the user in with their credentials so their mail profile just shows up for them, without them having to add the account. Without enrollment though, I don’t think that would work (because they have to identify themselves by signing into the app anyway).
In a MAM scenario were you want to release a new app or produce one. Publish it to the company portal. How would it be accessed in MAM perspective. As far as I know Company portal needs a managed device in order to fully functional – but maybe I am wrong?
If you have a need for company portal and custom apps, etc. ,etc. then you are talking MDM. You could still do MAM on top of that if you wanted to protect the app data in addition to managing the device. But in a MAM-only setup there is NO need for company portal or any of that nonsense. Users just go get the apps they want from the apple store or play store, and that’s it.
Hi Alex,
Thank you for detailed outline on Microsoft Intune MAM.Based on above threads, to leverage Microsoft Intune MAM, custom has to be applications wrapped with Intune app protected SDK and published in public store. This approach will not require MDM or device management policies on personal devices.
MDM is little heavy lift for the end users to configure on personal devices and security has push back on publish company application in public app stores.Is there any other options in Microsoft Intune to publish the custom company mobile applications in internal portal and allow end users to install the enterprise Mobile application from the internal portal with similar user experience like Outlook in public app store without MDM profile?
If you actually have custom apps then why wouldn’t you be doing MDM? How else would you push the custom apps out to devices? The Company portal app is where you publish the apps, and when users sign into the app it enrolls the device–I do not believe there is a “sign in only” option for the app–to my knowledge it kicks off the enrollment process when you sign in. Would be an interesting use case–something like “sign into the Company portal without enrolling the device.” Is this a feature request on Uservoice yet? Maybe check it out and add your idea if not.
Thank Alex.
Yes something like “sign into the Company portal without enrolling the device.” option.This will allow the users not to install MDM, at the same time company security is covered since the app is not published in public store.
But is an Intune license required for MAM-WE?
Yes–and Intune is included with Microsoft 365 Business Premium.
How does the policy “precedence” get decided when multiple MAM policies are applied?
Most restrictive settings win.