Updated! Checklist co-developed with Microsoft: Set up your SMB customers for secure remote working
I had the great pleasure to participate in a webinar today with David Bjurman-Birr (Partner Architect) and Jon Orton (Director of Product Marketing for Microsoft 365 SMB). David and I recently developed a checklist together for Microsoft 365 Business Premium, aimed at helping partners who work in the SMB space to configure their customers’ tenants for secure remote work with Microsoft 365, and especially Teams.
Eventually this will be more polished up and put out by Microsoft officially, but if you want to get an (editable) copy sooner, then you can grab the checklist here [Note: this link has now been updated to the official checklist released by Microsoft].
The following are some slides from the deck:

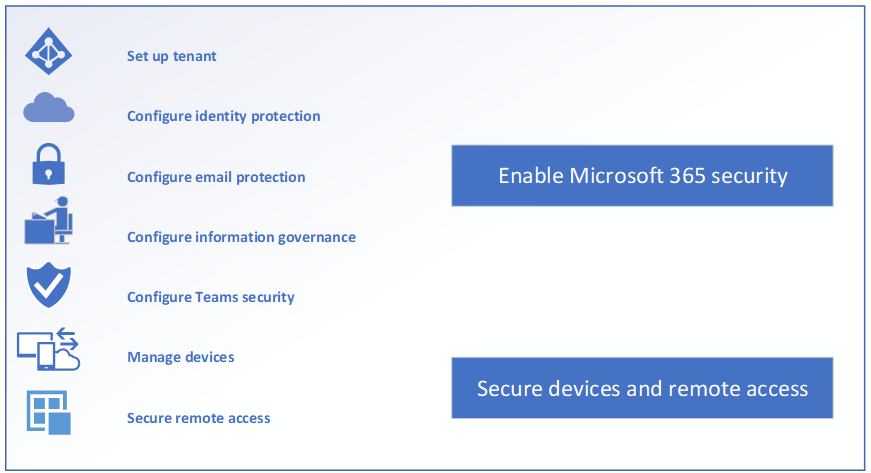
What? Only 4 steps?!! Well, sort of. Let’s expand this out a little bit.

Note: You should have Microsoft 365 Business Premium to completely implement the checklist.
Each step has a number of sub-steps to complete or at least consider. As well, we have given two examples of possible configuration values, depending on the risk tolerance of the organization. So for example, a local conservation club or small retail chain may not have as much interest in going deep on some of the security and information governance items, sticking with defaults and selections in the left column, whereas a law firm or medical provider would need to lean into the right column while they prepare their tenant and roll out Teams more carefully.

That might mean that the law firm turns on Sensitivity labels and blocks access to sensitive data on unmanaged devices, whereas the conservation club doesn’t have this requirement. As well, a law firm may need to disable Anyone links, and maintain a solid audit trail when working with external clients, partners, etc., vs. a non-profit like a conservation club who wants to distribute links to their materials far and wide in the community without a lot of friction to sign-in or authenticate.
The point is to illustrate that you have several options when it comes to security & compliance–it is up to you, the technology advisor, to review these talking points with the stakeholders. If you are a Microsoft partner or independent consultant, it is recommended that you familiarize yourself with these “risk profiles” and know how to speak to each line item–that way you can consult with your customers about the best level of risk acceptance for their unique scenario.
Update: See the corresponding blog post at the SMB blog in Microsoft’s Tech Communities. The list has been updated and expanded, with much more detail including helpful links that describe each part of the checklist.



Comments (8)
Excellent checklist Alex. Will the webinar be available to watch later ?
Yes–when they post it I will let you know!
Also a useful site for reviewing security setup for Teams:
https://www.microsoft.com/en-us/microsoft-365/blog/2020/04/06/it-professionals-privacy-security-microsoft-teams/
Excellent..maybe just add the licence requirements for some of the settings :)
Ah, I can update that–the recording will have it already–this has the SMB in mind, using Microsoft 365 Business (now renamed to Microsoft 365 Business Premium).
They posted the checklist on the SMB blog. I still waiting on the recordings.
–Tracy
I know, me too! I will bug them again this week.
We published the recording here: https://www.microsoft.com/microsoft-365/partners/videos/secure-your-smb-customers-as-they-cope-with-covid-19
Also – the ‘official’ version of the checklist is here: https://techcommunity.microsoft.com/t5/small-and-medium-business-blog/practical-guide-to-securing-remote-work-using-microsoft-365/ba-p/1354772
AND we made a partner kit available here: https://aka.ms/SMBSecurityKit