Poser alert: Do you think this may be leveraged for Social engineering? Or what…?
Interesting thing appeared in my WordPress comments over the weekend: it appears that someone lifted content from my blog and re-posted it as their own. Why or how WordPress picked up on this and alerted me via my comments is unknown at this time (maybe some WordPress geeks out there can explain it to me). I do NOT think this was a “pingback“–or at least it was not an intentional one.
Here’s a screenshot of what showed up for me:

I followed the link to his blog under the “Author” field. Here is a screenshot of his article on Safe Links taken 8/24/2019:

And for comparison, here is a screenshot of my website (same article):

He even uses the same screenshots, which contain my initials “AF” in the upper right corner where your avatar or user initials display in the 365 portal. The dates do not match here, but in this case at least, his is dated a few days after mine (even though I know this content went up just this weekend).
Scrolling down further on his blog, in the same post, I find some additional content that is not from my original post.

But again here the screenshots actually contain clues as to the original content creator–https://oodwar.moe — which actually appears to be another really solid resource.
Nowhere on this page did I find any credit being given to either myself or Oddvar. I decided to attempt contacting this poser, and asking him what the deal was–I mean this is poor form–if he was going to re-post content without asking first, he should AT LEAST attribute and give credit where credit is due. His website is looking pretty sparse overall but does feature a Contact page that only points to a LinkedIn profile.

Following the link, I see that this person apparently works for Microsoft.

Russell Bagby, “Senior Office 365 Azure Support Engineer II.” But his title makes very little sense to me. And, as it so happens I had been corresponding with multiple employees at Microsoft lately, so I decided to ping a couple of them. I got a couple of responses within an hour, confirming my suspicions, that this person does not work for Microsoft at all.
Interesting. I have a pending invitation out to him on LinkedIn, we’ll see what happens there. In the meantime, I also reported this person via that “More…” button you see in the screenshot above. I suggest you do the same–he might not even be a real person, but he is at least misrepresenting himself as a Microsoft employee.
I returned to some other research on his website. He does also have an About page that references his alleged employment at Microsoft as well as another link to his profile at LinkedIn.
I also looked over another one of the posts he lifted from me. The first I examined was his plagiarism of my Safe Links article, and the second one I found was about Safe Attachments. Here I found more interesting details.

Again he back dates the article, this time all the way to February 2017. More than a year and half before the other post, and therefore pre-dating my original by quite a long time. We have another of my screenshots featuring all the original text from my website, reprinted as his own of course, but at the bottom of this article, hilarity ensues–he has used that same bit from the Safe Links article at Oddvar’s site again! But wait a minute, wasn’t this article about Safe Attachments?

I am starting to wonder how hard this guy is really trying… or how much of the content that he is lifting, does he really understand?
Just out of curiosity, I did a quick whois lookup on his domain.
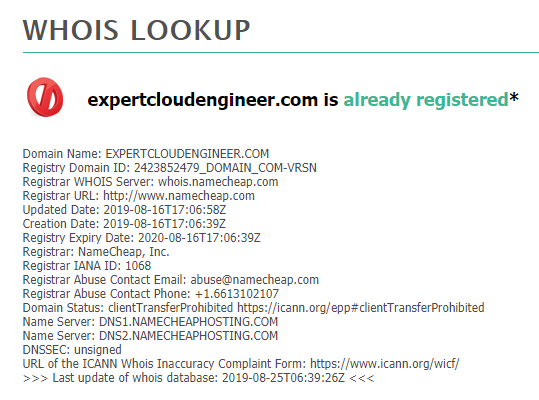
Oh wow, look at that creation date–08-16-2019. So this thing is like a week old. This stuff is indeed just being slapped together now. I did send an email to [email protected]–but I’m not sure if that will go anywhere. It would be difficult to prove ill intent here, but on the other hand…
My theory
Let’s review the facts:
- Dude says he works for MSFT
- MSFT says “nope, not ours”
- Has several posts relating specifically to Microsoft security products that admins would be using to protect their tenants
- The posts aren’t legit, and are in fact stolen from other sources
- Back-dated everything to make it seem like he has a longer track record than he actually does
Sure seems suspicious right? What could someone do with this kind of a platform? Here are two of my guesses:
As a way to establish a trusted authority — which can be leveraged in social engineering schemes either online or in person. Think about it, wouldn’t you trust a Microsoft employee who is just trying to “help protect you?” Would you give them information, go to a website, or click on something if they asked you to?
As a way to apply for jobs they may not otherwise be qualified for — This person may not actually mean harm, he might just be trying to break into a field that he appears not to know that much about, but you know, if you get “in” first you can usually figure it out, between helpful blogs like mine, which he has already pre-mined, and on-the-job training (lol)
I’ll throw a further-fetched idea out there. There have been cases of state-sponsored online personas, who for example, posed as legitimate journalists, quietly mimicking U.S. news outlets for a number of years leading up to the elections, then started spreading “fake news” as the elections drew near. They were so well established and trusted at that point that nobody questioned the headlines they would Tweet out–and they were almost always aimed at “riling up” each side against the other, trying to drive a wedge further and further between the parties. More polarity leads to greater instability: a house divided against itself cannot stand.
This kind of thing has been cracked down on a lot, but it continues to be exploited nonetheless. Indeed, its hard for social media giants like Facebook, Twitter and others to stay ahead of it.
What if this is another attempt by foreign powers to infiltrate America? It’s more subtle than using fake news outlets and journalist personas as handles. If they have several hundred of these more “normal” fake people who seem to be legit citizens and have websites, LinkedIn accounts, and who knows what else–they can become mouthpieces that spread fake stuff and hateful materials, misinformation, bad links, malware, or are just generally used as assets to disrupt and contort information and drive more disagreement and confusion among the populous at large.
Okay, that may be a more far-fetched theory, but there is an election year just around the corner… so…
In any event, I just cannot think of a legitimate reason for someone to have taken the trouble to do what they did here. How would this ever be used for anything but evil? I urge you to go to his LinkedIn page and report him, at a minimum. Tell your friends, too, if you care to. And stay wary out there–it occurred to me that I have recently seen some other people attempt to friend me on LinkedIn claiming that they work for my employer, when I know they do not. More fake people? Hmm… Be sure to do your part to shut this stuff down whenever you become keen to it.
Any other thoughts or ideas you want to share? Drop me a line or leave a comment here to let me (and others) know.
Last note: I also wondered why it is that WordPress allows you to back-date articles like that. Seems like a risky feature that should be eliminated. Make timestamps matter! This could become more and more important for all publishing platforms. Imagine if you could send emails into the past, as a famous Google hoax once claimed– the World would lose its mind, and email would lose credibility.



Comments (5)
He is probably a scammer and creating fake credentials and experience for himself in order to fool other people he is trying to scam somehow. Come on…look at his LinkedIn pick! haha
Maybe there is somewhere on one of his pages or profiles you can put in a complaint so he can be taken down if he is doing it for scamming reasons.
On the bright side, he is plagiarizing the best!
I would rather believe this is an attempt to drive traffic to his website and earn on ads or something. About back-dating. WordPress is a CMS and all CMSs have this feature, because it is too often when something needs to be posted with a back date :) I don’t do this myself and i always found this silly when PR was posting a news piece they forgot to post a few weeks ago with the “original” date. But they have various reasons (usually some regulations, fines, etc.). You can find out through the logs or some internet archive systems, but not many will go that route to find out the real date. There can be some legitimate reasons, like rebuilding old site and wanting to keep the original postings timeline, etc.
This is a real shame. I appreciate very much your hard work and willingness to share your talent with those of use still learning to use O365 effectively. Here is a site that has some suggestions about plagiarism prevention that may be useful. https://mhthemes.com/blog/fight-plagiarism-wordpress-blogs/
Even if they removed the feature to change the post date, you can just change that directly in the database.
You could also file a DCMA request to get the website taken down.
I’ve done that a couple of times (after contacting the offending site) to get the entire site down.
The curious thing is that he is copying multiple sites into one site so it’s not a bot just grabbing your feed and dumping it into their own site.
Having said that, it would be pretty funny if it was a bot that then reposted this page too.