Inventory and Control of Apps within and beyond the perimeter with Microsoft 365
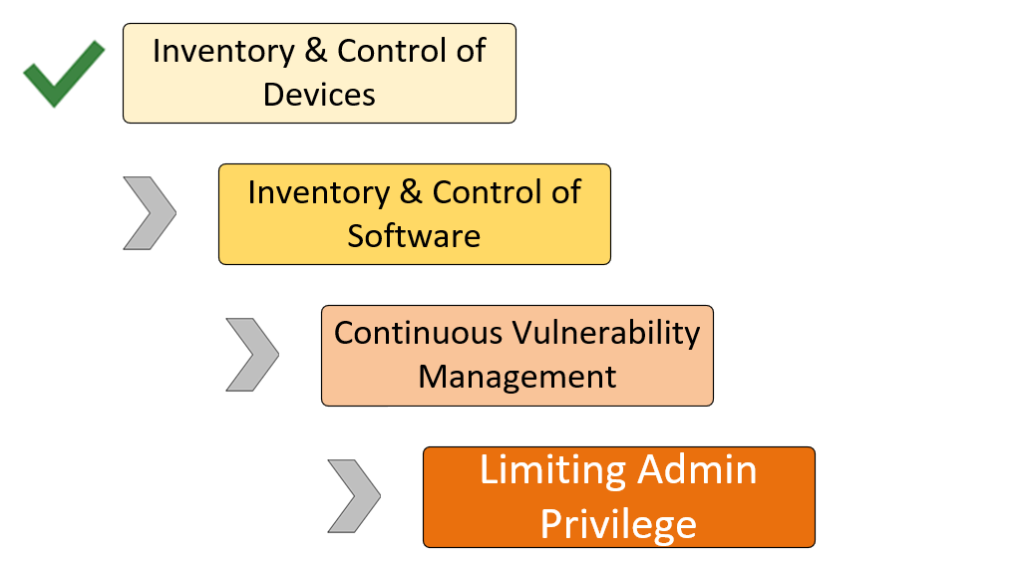
Managing devices is a topic I have probably burnt my readers out on by this point, so it’s time we move into the next stage: wrangling all those crazy third-party applications hiding out in your environment! To build up a foundation of good security, we must identify our apps and determine what is approved and not approved, and how to take governance actions against apps that are both sanctioned and unsanctioned.
The key that unlocks all of this is Cloud App Discovery, available with Azure AD Premium P1 (now included in Microsoft 365 Business Premium) and Microsoft Cloud App Security (MCAS). And, for those out there who want even more security superpowers, we should discuss some important integrations to Microsoft Defender ATP, which is also now available as a standalone subscription that can be added to Business (it also exists in Microsoft 365 E5 or Microsoft 365 E5 Security).
Cloud App Discovery
If you visit the Cloud App Security portal (portal.cloudappsecurity.com) you will find a place to discover all the various applications sending and receiving traffic in your environment.

This is an amazing tool that allows you to gather data about apps that you may or may not know about in your organization. You can even get some good information about compliance related concerns for each discovered application.

The above data (under Discovered apps) displays the applications that exist in this demo environment; applying a couple of quick filters and sorting based on “Score,” I can already see that some of them might pose a higher risk for the organization. Not all cloud apps will meet your compliance requirements, and this tool can tell you quickly which ones you should be looking to block and replace.

For example, if you wanted to meet ISO 27001, FINRA, or ITAR–you’ll need to replace this app!
Data gathering
Where does all the data about what apps are being witnessed in the environment come from? One of two places:
- Firewall (e.g. uploading logs from your edge device)
- Endpoints (via MDATP)
The first option is available with a Microsoft 365 Business Premium / Azure AD Premium P1 subscription, and we can gather the data either as a snapshot (this is a one-time upload–which is a great tool for assessments), or you can have it shipped to MCAS automatically via syslog or similar when you want continuous monitoring. Just use the ellipses in the upper right corner to find these options.

Now, just take a look at the current situation with this pandemic. Much less traffic than ever before is routing through your traditional corporate firewall–and even before the pandemic, this was the trend: work happens everywhere, and we’re more mobile than ever. Therefore the best way to get this data is from the endpoint–but to do that requires a subscription to Microsoft Defender ATP as well as Microsoft Cloud App Security.

Once you have the licenses applied, from the Microsoft Defender Security Center (securitycenter.windows.com), go to Settings > Advanced features to enable the integration and allow MDATP to send its endpoint data to MCAS.
Note: You must license all your users even though the functionality opens up with a single license applied to the tenant (users who benefit from features must be licensed for the features)!
Blocking apps
Microsoft 365 provides a lot of functionality and tools that people historically went out to get on their own. Do you really need DropBox or other file sharing apps if you have OneDrive, Teams and SharePoint? No, probably not. And there are many other examples of apps that can be re-evaluated and replaced with alternatives in 365 platform, too!
But after you put out the message to switch over to the approved corporate apps, how do you enforce the policy? Two choices: one, remove local admin privilege–this is a great way to reduce your overall risk anyway and you should be working toward it. This can be done easily with Autopilot, which is a feature of Microsoft Endpoint Manager (Intune)–included with Microsoft 365 Business Premium.
Second option: if you leap for the extra security bundles, MCAS will allow you to block apps and this can (again) happen in one of two ways:
- Firewall (generate a block script that is applied to the device)
- Endpoint (built-in integration using MDATP)

To use the firewall option, pick the ellipses in the upper right corner of the Discovered apps page and click Generate block script, after marking apps as unsanctioned.

The block script will need to be applied to your edge device in order to block the apps. To enable the MDATP integration, visit Settings > Microsoft Defender ATP and tick the checkbox.

You will also need to enable one more option under the Advanced features in Microsoft Defender Security Center called Custom network indicators. This allows the MDATP service to tell endpoint devices to add custom URL’s and IPs to the block list using Defender’s Network protection capability.

Assuming you configured the integrations as described above, MDATP will handle the rest, communicating the information to endpoints. Users would not be able to use these apps anymore on their Windows 10 devices.
Pretty slick, right?
Of course, if an app IS sanctioned even though it is third-party, we also have the option to bring these other apps under management using Azure AD for Single Sign-on, adding more security while adopting them into the corporate fold. This is also available natively in Microsoft 365 Business Premium.
However it is also worth mentioning that Microsoft Cloud App Security can take your management further for several popular third-party apps, by monitoring logs and governing files and activities via policy–the same as we do for Office 365. Proxying traffic via MCAS, you can then also enable Conditional Access App Control policies (another integration with Azure AD Premium).

Overwhelmed?
I know, it’s just crazy how many security tools are in Microsoft 365, right?! Yes, it is pretty gnarly. But I like to think that it is gnarly in a good way. This is just one powerful example of how the various pieces of Microsoft 365 can work better together.
If you were building your own security solution, and wanted to include an EDR (like MDATP) as well as a CASB (e.g. a Cloud App Security Broker like MCAS), these would be two different tools that do not communicate with one another, and do not necessarily link back to your identity provider, either. With Microsoft 365, these and more can all be had in a single pre-integrated bundle, and they layer seamlessly on top of your Office 365 and Windows 10 investments.
Although the fancier part (MDATP to MCAS integration) requires additional subscriptions on top of the normal Microsoft 365 Business Premium SKU (details in the table below), I would argue that it is worth a closer look if you are an MSP working out how to provide a valuable service with Microsoft 365 for your customers that can also result in additional monthly recurring revenue.

You can add MCAS in a number of ways to Microsoft 365 Business Premium: as a standalone subscription or bundled in other packages. Maybe we will see some more of this stuff trickle into the Business sphere eventually, but for now, this is where it’s at.



Leave a Reply