Differences between Azure Information Protection labels and Office 365 Sensitivity labels
In the previous two posts, we looked at two capabilities of Azure Information Protection (AIP) P1, which is one of the many subscriptions bundled into Microsoft 365 Business:
Recent announcements have shifted the sands a bit here with so-called “Unified labeling“–which refers to a separate data classification system that is found within the Office 365 Security & Compliance center.
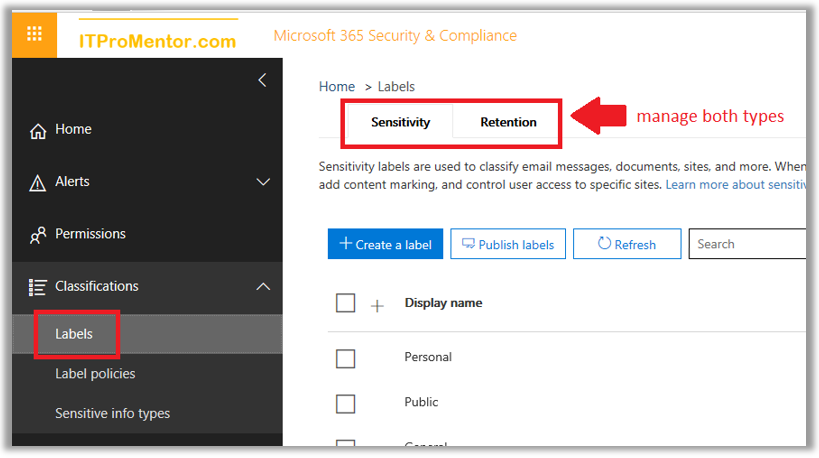
Through this UI, you can manage both Sensitivity and Retention labels.
- Sensitivity labels are used to apply encryption and protect content from being overshared (similar to AIP), for example you may want to label an email or document as Confidential and prevent accidental sharing with recipients external to the organization.
- Retention labels by contrast are used in situations where you want to preserve and/or delete content after a certain amount of time has passed (e.g. content expires and is removed after 7 years). We won’t cover these label types in this article–another time.
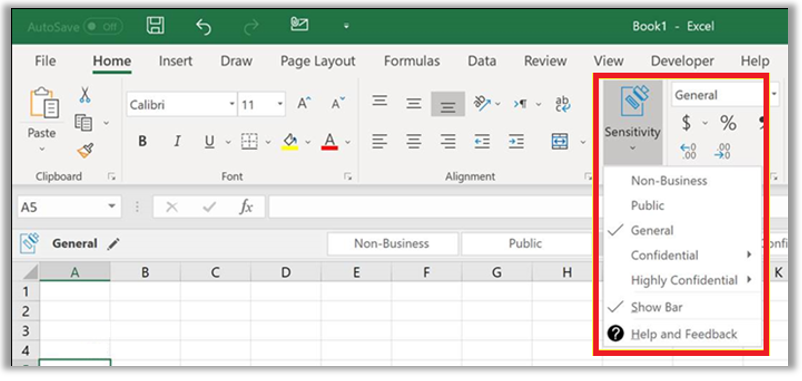
Along with the Unified labeling announcement came the news that your AIP labels can be carried over into the Office 365 Security & Compliance center’s Sensitivity labels. Soon in 2019, the Sensitivity button, which allows users to stamp individual files with these classifications, will be deployed into the Office applications (actually they are starting to show up in certain places already–such as Office 365 for macOS).
But there are still important differences between the AIP labels and the Office 365 “Sensitivity labels,” even though they can now be kept “in sync” with one another. As we move through this article, I will try to clear up the differences between these two label sets.
Migration from AIP to SCC Sensitivity labels
If you make the move to “Unified labeling,” you still need to use the AIP client for the time being. I know, wah-wah. Bummer. However, once the Office applications have native support for Sensitivity Labels, the AIP client will be optional–you would not need it in order to apply your labels/classification.
The migration feature is still in preview at the time of this writing but know that this process is also optional; there is no rush to move away from AIP.
Now if you are brand new to this, and have not configured labels in either portal yet, then completing this unification process with the default templates is pretty painless. Literally, it requires pressing just one button (see below).
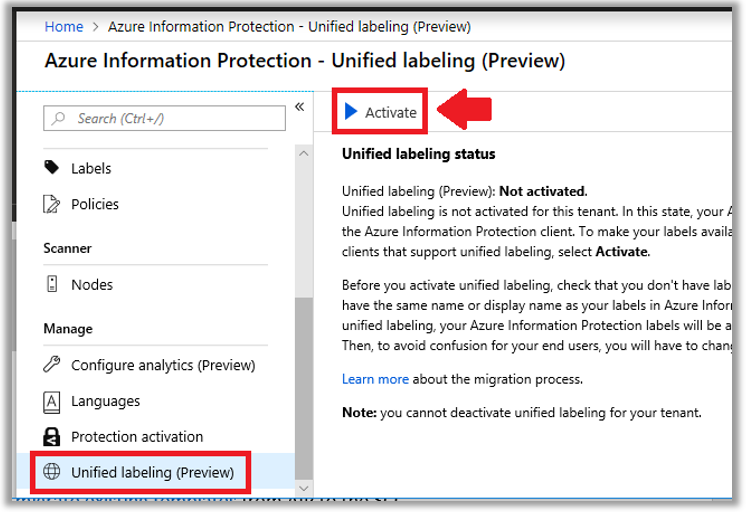
Otherwise, see Microsoft’s article describing how to migrate existing labels from AIP to the SCC, for some other guidance and caveats.
With that in mind, once you complete the unification you are free to create your own labels in the Security & Compliance Center, and access them using the AIP client. To get started in the Security & Compliance Center, navigate to: Classifications > Labels.
Planning data classification
Similar to what we talked about with AIP labels, planning your data classification with the stakeholders in the business is a crucial step which is often neglected. As an IT Pro you should be transparent with the business owners and decision makers about your capabilities with this tool, and clearly define the meaning of each data classification label.
You have these options via the SCC (they are not 100% the same as AIP):
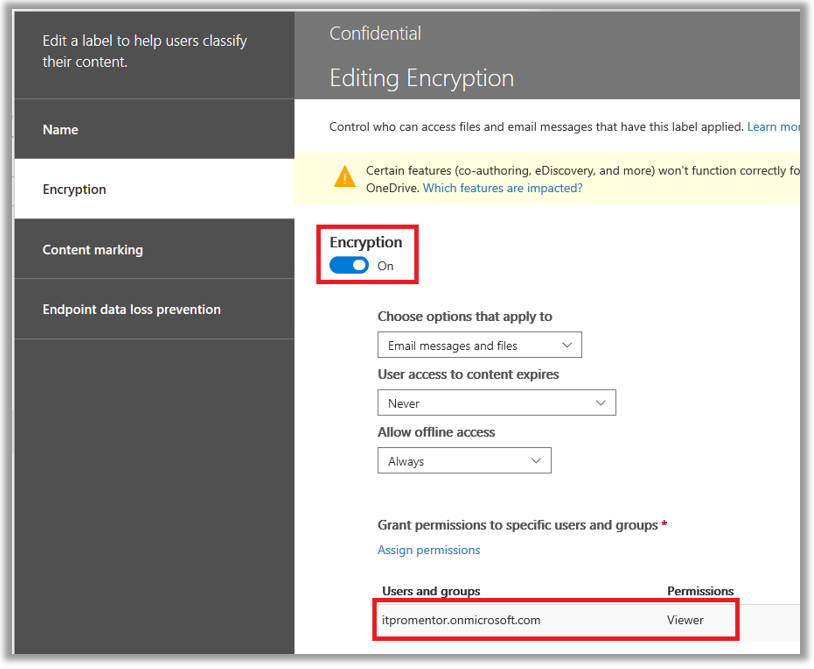
- Encryption – With the encryption option enabled, you can automatically expire access to shared content, allow or disallow offline access, and assign different permission levels to different groups of users. Templates include Co-Owner, Co-Author, Reviewer, Viewer, or, create Custom permissions.
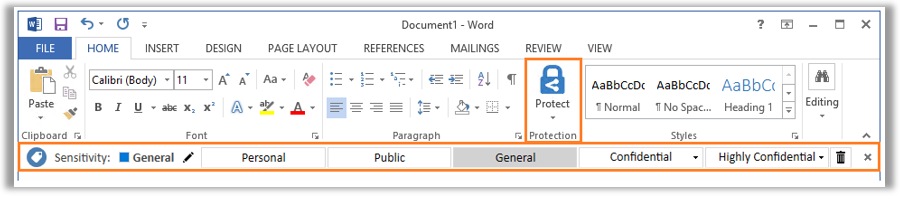
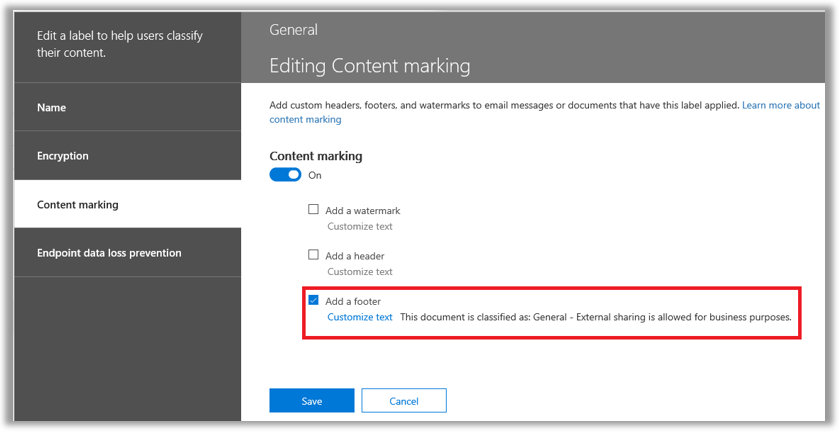
- Content marking – Apply headers & footers, and/or watermarks that clearly label the nature of the content on the document.
- Endpoint Data Loss Prevention – As of today, you would need a higher subscription level such as E5 to take advantage of this feature, see pre-reqs here. We won’t describe this in much detail except to say that when enabled, it signals to Windows endpoints that this data is extra sensitive, and cannot be copied or moved to say a USB device or other unsanctioned location.
In planning your labels, you may for example choose to enable only a header or footer on classifications such as General. No other protections such as encryption would be necessary, most likely.
However, for more sensitive content, such as Confidential, you may choose to use a watermark, and require encryption, limiting the permissions so that recipients cannot modify or redistribute content outside the organization. Note: the data owner always maintains full control permissions.
Last note: the order in which these labels appear in the admin portal does matter–just like with AIP. Why they don’t show some sort of sensitivity scale or something along the side is odd, but in fact, the “top most” label on the list is the meant to be the least sensitive, while the labels down at the bottom of the list contain the most protection and the most restrictive settings.
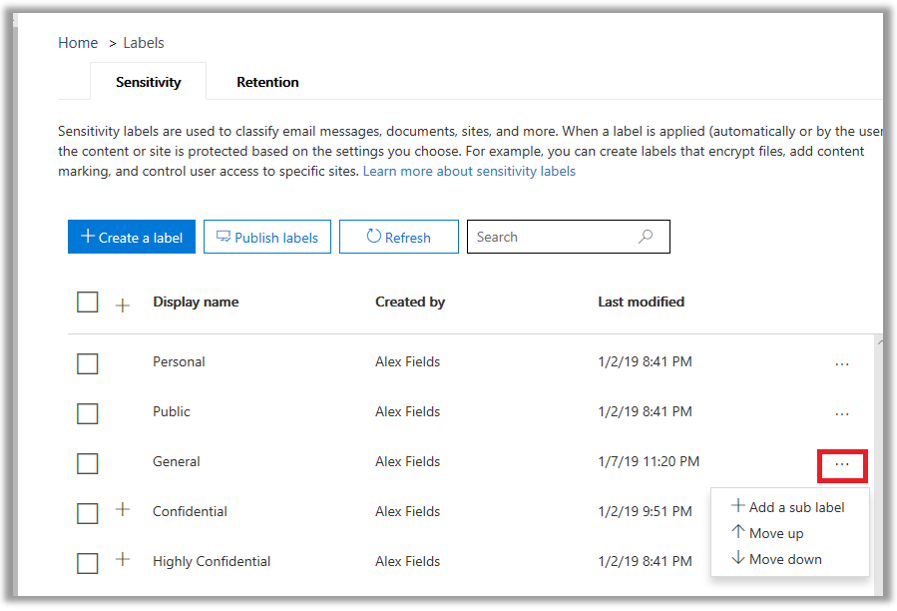
Creating your own label
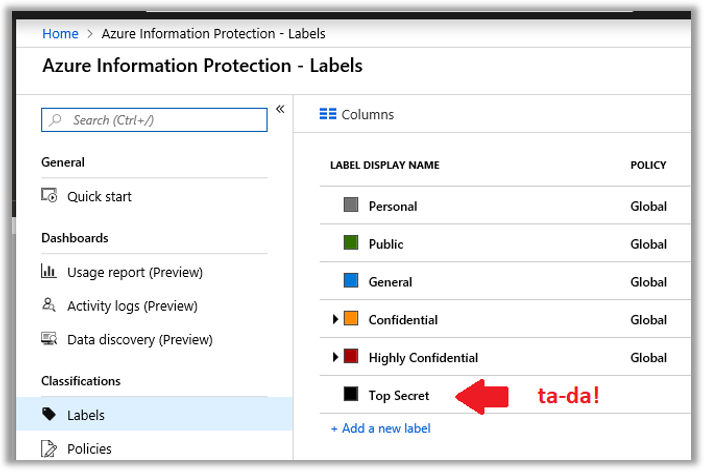
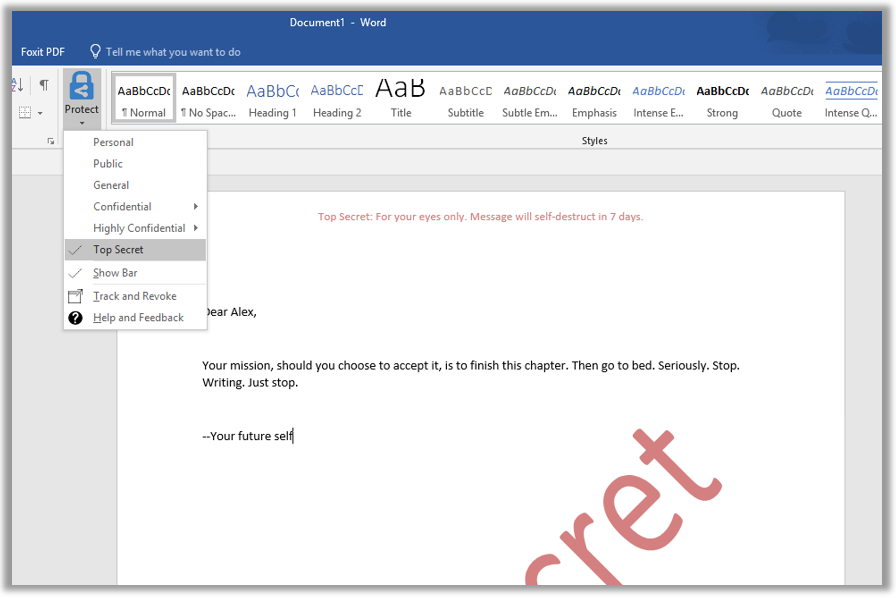
Let’s just say that you are going to create your own labels. I have migrated the default labels from AIP, but maybe I want to add an even more restrictive “Top Secret” label to the tail end of the labels list… because I have so much Top Secret data that I work with, and I’m feeling all Top Secret today. Like I’m in a Mission Impossible movie.
Let’s step through this process, by way of example. Click + Create a label to get stared.
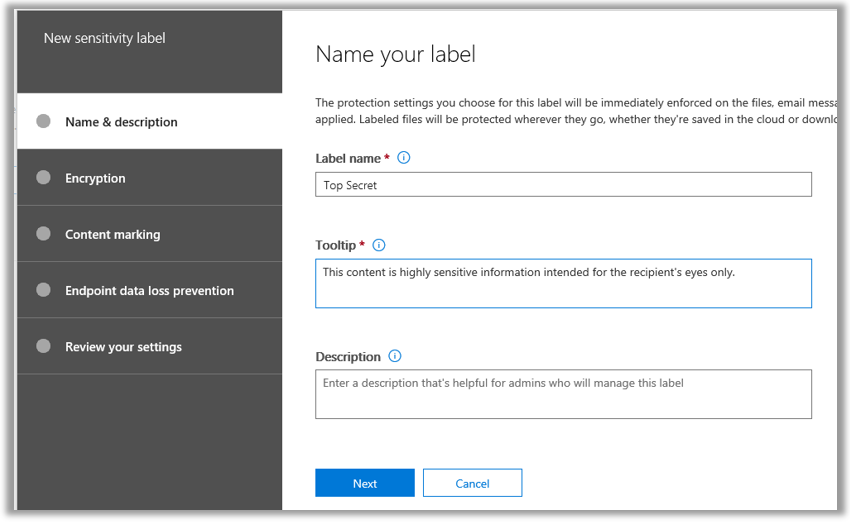
It is required to provide just two things here—a Name, and a “Tooltip” which is the short description that shows up on the bar or banner at the top of a document or email message when the label has been applied. Next.
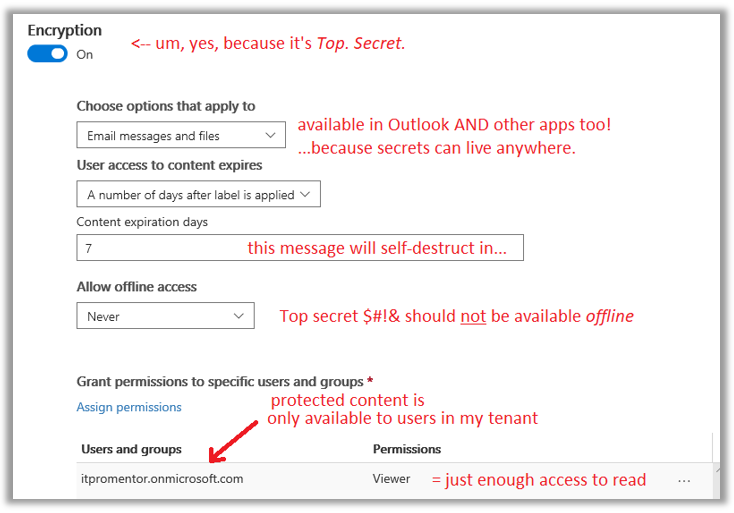
On the Encryption page, we need to make some choices.
- First of all, yes—we want this turned ON. It’s Top Secret, after all.
- Second, User access to content expires: We can force the content to expire after a period of time has passed, or not. I think, since we’re talking about Mission Impossible here, a self-destruction option feels best.
- The Allow offline access bit sounds scary to me. There is some black magic going on here which allows a user to authenticate once and then keep the token locally to re-open the document for a certain number of days without also re-authenticating, even if the endpoint goes offline, but I like the scenario where this is not allowed not happen much more. Given the Top Secret nature of my data and all.
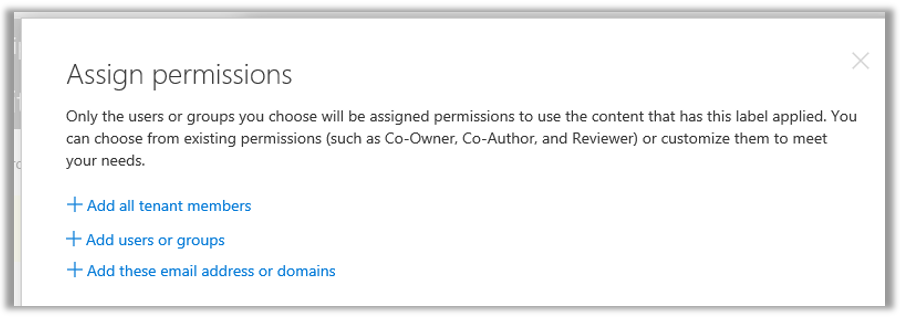
- Last, click Assign permissions to assign various users, groups, domains, outside email addresses, etc. various permissions levels. For this example, I am allowing recipients who belong to my organization /tenant the Viewer permissions, which contain just enough access to read the content, but do nothing substantial with it—edit, export, copy, print, etc.—all disabled.
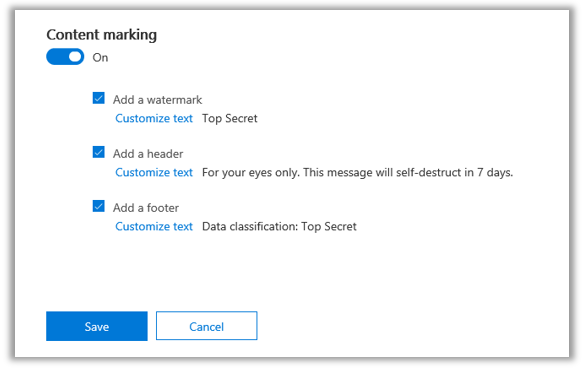
On the Content marking page, I am going to mark the crap out of this thing. Watermark? Check. Header? You bet, in Red text no less. Footer? Why not? One more reminder about the sensitivity of a document never hurt anyone when it came to TOP SECRET information.
Now, Endpoint Data Loss Prevention. As I mentioned, this would not apply to the Microsoft 365 Business subscription, at least today. Maybe things will change in the future, but right now this would require Windows Information Protection (WIP) and Windows Defender ATP—which are available only at the Enterprise E5 level. So do not configure this option and just Save and Close after reviewing your selections.
Next, if you want to verify that the marriage between your AIP labels and the Office 365 labels is working correctly, go check out the Azure portal.
Publishing the labels
Once you have your labels all defined, you will want to publish them to your end users. It is possible to publish different sets of labels to different people, but many small businesses will simply publish all the available labels to everyone. Click Publish labels to get started.
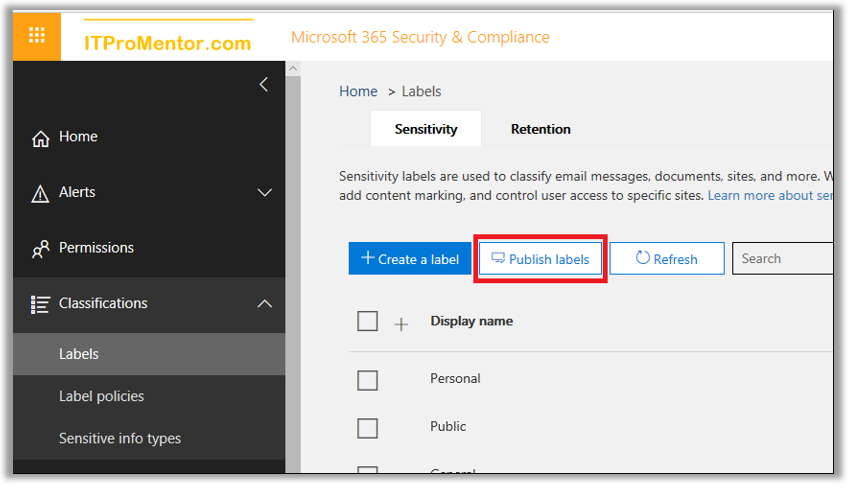
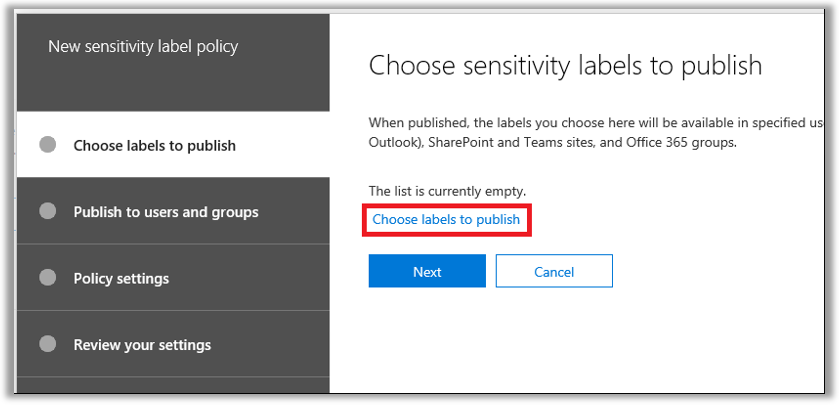
Click the link to Choose labels to publish. Select all the labels you want to publish and click Add. Next.
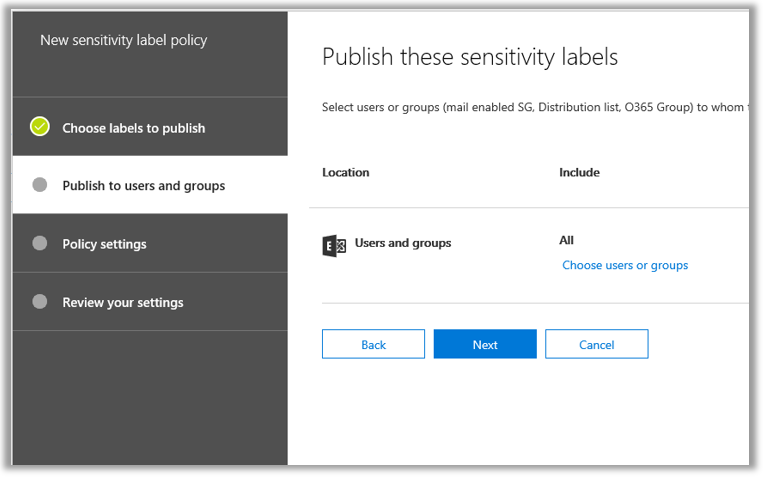
Choose users or groups to whom these labels will become available.
Next, on the Policy settings page, we find that it is possible to choose a default label which is applied to new documents or messages (or leave it set to None in case you do not want this behavior).
As well, we can require users to provide justification when removing or “downgrading” a classification. I would recommend this setting, certainly.
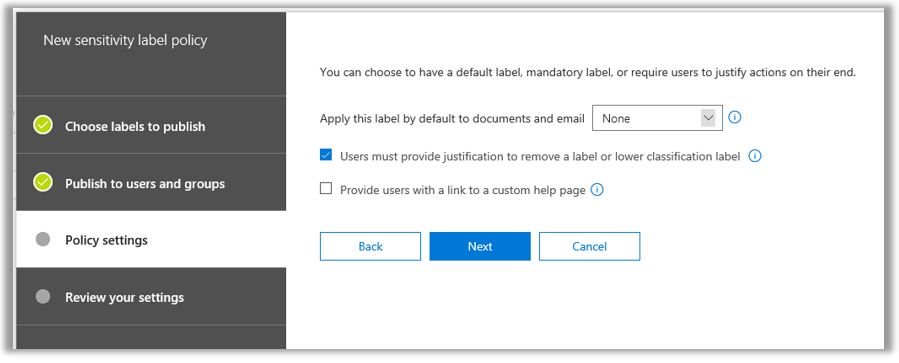
Last on this page, I don’t know that many small businesses would take the time to develop a custom help page for sensitivity labels, but maybe… and IT Providers… this might be a cool thing to develop and give to your customers.
Working with labels in Office
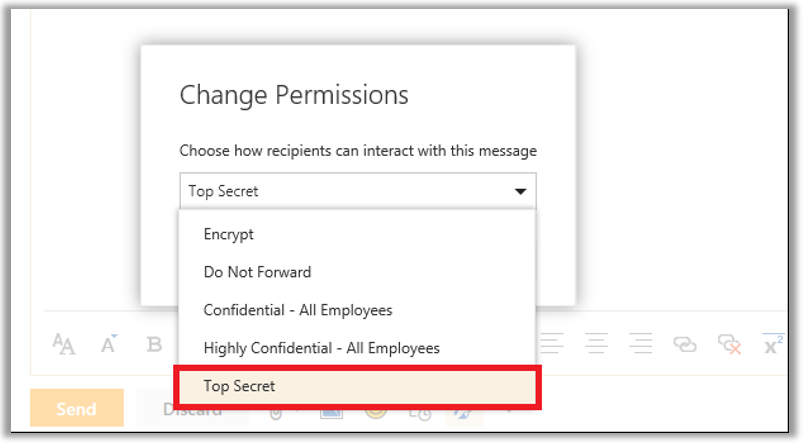
Now, if you have previously configured the Protect button in Outlook using PowerShell, then you will find that your new sensitivity label is already available to use in Outlook on the Web.
As mentioned previously, to label content in the other Office apps will require the Azure Information Protection client to be installed on the workstation, for now. The AIP client is available from Microsoft downloads. And yes. There is an MSI that you can deploy administratively.
Once installed, the next time you open your Office application, you should see the Protect button. When I label my document as Top Secret, the watermarking and permissions I expect are applied.
AIP labels vs. Sensitivity labels
If you decide to stick with AIP for now—that’s totally cool. But even though you can “unify” the two disparate label sets, it is important to remember that they are not the same. Azure Information Protection is a more advanced subscription with more capabilities than what exists using the Office 365 Security & Compliance center’s “Sensitivity labels”—again, at least for now.
The main difference to note is that AIP is better suited to hybrid environments. You can use the AIP client to encrypt documents on a traditional file server, for example, right in Windows Explorer.
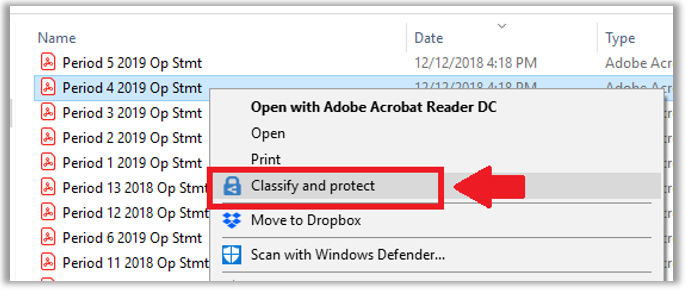
Therefore, AIP works whether you have Office 365 or not—you could even buy it as a standalone subscription and use the client to classify content on any server, or in any cloud. Office 365 Sensitivity labels, by contrast, are specifically available with Office 365 apps.
Another notable difference: as we go to configure protection settings on a label in AIP, we will find an option to either Set permissions administratively, or, to Set user-defined permissions. There is no equivalent to the second option within the SCC wizard: In Word, Excel, PowerPoint and File Explorer prompt user for custom permissions.

That is to say, the Office 365 Sensitivity labels do not appear, at this time, to support user-defined “Custom” permissions, as the AIP client does.
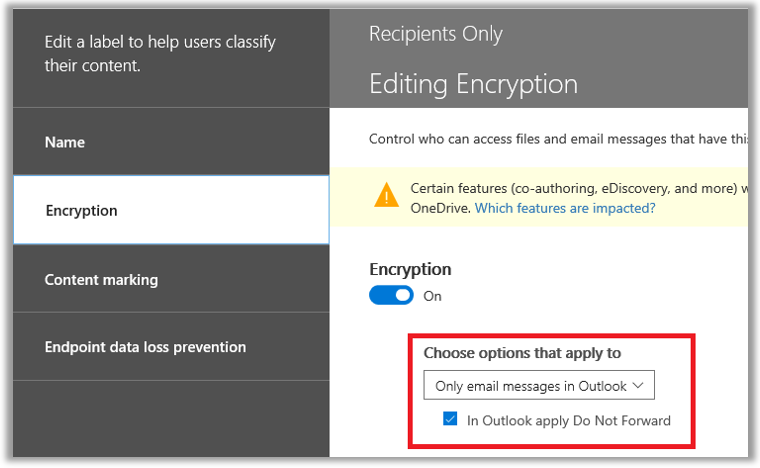
Now if you were to choose ONLY the first checkmark box above: In Outlook apply Do Not Forward, then that would be equivalent to choosing the Only email message in Outlook option with the corresponding checkmark box for Do Not Forward in the SCC wizard. But again, the second option to allow the users to specify custom permissions within the other apps–doesn’t exist.
Now back in the Azure portal, if you assign permissions administratively, using Set Permissions on the Protection blade, then in specifying users and groups for the recipients of a labeled document we find an option called: Add any authenticated users – you know, people who might be outside of your tenant?
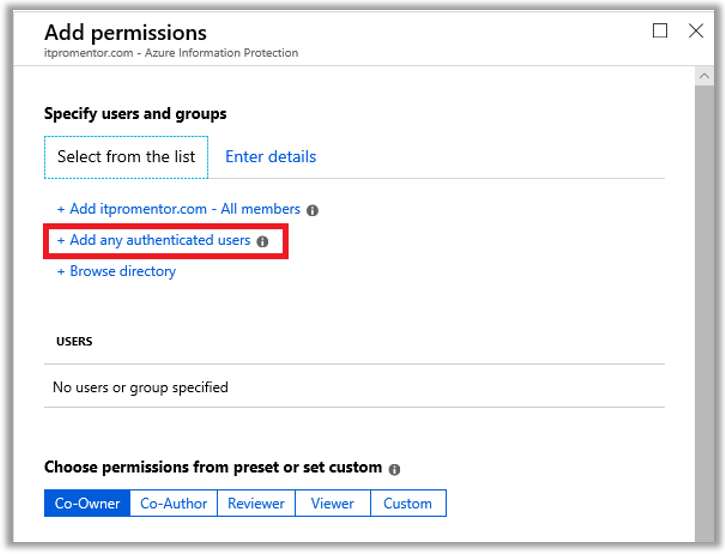
From Microsoft: This setting doesn’t restrict who can access the content that the label protects, while still encrypting the content and providing you with options to restrict how the content can be used (permissions), and accessed (expiry and offline access).
However, the application opening the protected content must be able to support the authentication being used. For this reason, federated social providers such as Google, and onetime passcode authentication should be used for email only, and only when you use Exchange Online and the new capabilities from Office 365 Message Encryption. Microsoft accounts can be used with the Azure Information Protection viewer and Office 2016 Click-to-Run.
Some typical scenarios for the any authenticated users setting:
- You don’t mind who views the content, but you want to restrict how it is used. For example, you do not want the content to be edited, copied, or printed.
- You don’t need to restrict who accesses the content, but you want to be able to track who opens it and potentially, revoke it.
- You have a requirement that the content must be encrypted at rest and in transit, but it doesn’t require access controls.
Again, there is no equivalent to this in the SCC. You can add external email addresses or domains (and this same capability is also present under the Enter details tab in the AIP blades), but the lack of the “Any authenticated user” option means that you, the administrator, would need to know in advance any potential external users that would fall under the scope of this label.
Handy for sharing with known partner organizations, but not very helpful for allowing users to distribute protected content to anyone (well, anyone with a Microsoft account and AIP viewer, anyway).
Last, as we go to publish our labels via a policy, in the SCC we will not find the toggles to control extra buttons that show up in the ribbon, including the Do Not Forward button, as well as the option for users to apply their own custom permissions.
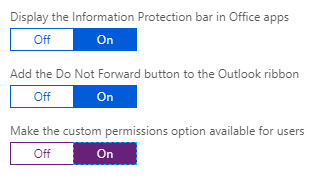
This makes sense since, again, the SCC interface would not contain settings for the AIP client. Time will tell if the built-in Sensitivity functions will include support for extra buttons such as Do Not Forward (or Encrypt?) in the future.
And there are other differences. For example, in the P2 subscription of AIP (e.g. available in E5), you get access to auto-classifications–if certain sensitive data types are detected, content could be automatically classified based on conditions. There is also an on-premises scanner which can find and classify sensitive content on traditional file servers. But as pertains to the Microsoft 365 Business subscription, I think I have identified most of the significant differences here.
Hopefully these articles have given you some ideas about how to use the Azure Information Protection features with your subscription, and clarified the confusing new “Unified labels” thing as well.


Comments (53)
Very helpful post thanks!
May I ask just one additional question? Would you know if in the future, SCC is supposed to completely replace AIP (at least once the feature gap is filled)? If a customer is not yet using either SCC or AIP but wants to start classifying content, would you recommend to start directly with SCC or still use AIP even if they may need to migrate to SCC in the future?
Thank you,
Personally I’ll keep using AIP, but I have a majority of customers still in a hybrid scenario, with local file servers, etc. And that won’t necessarily disappear overnight. The AIP client is nice for its Explorer integration. I do not know, and would be surprised, if this functionality ever came to the built-in labels in 365–I think they are made specifically for content residing there (SharePoint Online, Exchange Online, etc.). If you had a customer who was well on their way to cloud-only, managed and hosted content in 365, maybe just move forward with the new sensitivity labels.
SCC will replace AIP for label and policies management. Currently you can activate the unified libelling in AIP and in this way to make your labels available in SCC. Later this year we will auto-activate unified labelling in all AIP tenants.
North star is: one portal to manage labels (SCC) and all clients get their labels and policies from their (native labelling in Office or UL AIP client).
Awesome, thanks Denis! Hopefully by then the AIP features which are missing from the SCC will be available, such as the ability to specify custom/user-defined permissions.
Thanks for the feedback!
Regarding the Explorer integration, I have tested the AIP unified labeling client (preview version) without even touching AIP or the unified labeling activation setting, just using SCC sensitivity labels and it works: I have access to my labels from the explorer and I am able to apply them to my documents even outside a OneDrive folder. I’m however not sure to know what it means for the future. I guess only Microsoft folks know… (or do they? ;-) )
Oh interesting–so you didn’t even have to “unify” your labels first. Well, that’s cool.
Question:
Is sensitivity label and retention label can work simultaneously?
Yes, you can apply both sensitivity and retention to a document. It used to be that they were going to combine these two functions into a single label, but there were a lot of complaints about this idea from the community. Can you imagine the multiplication of labels that would create? “Well this label is for Confidential (All Employees) and it does 3 years retention, but we also need a 5 year option. Then the finance team needs a confidential / 7 year label and a 3 year label and a 5 year. So separating them made more sense, because you don’t have to create multiple labels that apply the same rights for various lengths of time. Instead you can apply permissions independently of retention–which is way better.
How to apply sensitivity label and retention label to SharePoint document library?
It’s coming native to those interfaces, but not yet. For now, use the AIP client.
Hi. Alex. Great article. So does this mean that my Office 365 Business Premium customers do not need to purchase the AIP ad-on in order to encrypt emails they send and encrypt documents? I was told by Microsoft that AIP is required in order to encrypt emails.
AIP is one of the supporting technologies that make the sensitivity labels possible, so yes you do need that subscription. Microsoft 365 Business does include it, but not Office 365 Business Premium on its own.
See this link for more detail
Great information, thanks for taking the time to write it!
An amazing amount of detail. When you say configuring the Protect button with PowerShell what are are referring to?
It is actually now the “Encrypt” button. When you enable it, there is a button to click that will apply OME to the message.
Do you mean the Sensitivity Button? If so this doesn’t seem to locate the UL policies under the tenant of the current switched user. Under Sensitivity -> Help and Feedback it still shows the original installation count for Office. I have raised a support call with Microsoft to track the progress of this issue…
The protect/encrypt button is something you can enable in OWA. See this article. The Sensitivity button is a separate thing–it will eventually show up in the apps for the desktop (it is already visible in MacOS versions of the apps). The sensitivity button will display labels, but only the labels that are visible in the security & compliance portals. It can’t see any labels in Azure/AIP. If you activate the unified labeling, then that process should copy all the AIP labels into the sensitivity labels in 365. That way the sensitivity button could expose the same list of labels as the AIP client.
I have done this now and reported to the compliance team a number of show stoppers I have found when conducting experiments.. 1) not being prompted when downgrading a sensitivity label. Not have an efficient way to set default retention and sensitivity labels . Set-PnPListItem only works when using AIP “classic” labels and not UL labels. Indeed these are not even shown in the document info panels in OneDrive or SharePoint online. MS SUport suggest Cloud Application Security as an efficient alternative. Tests on gong …. ;-)
Yes, I have been sticking with AIP for now. Supposedly they will close up the gaps later this year, but we’ll see. I still feel like it has a ways to go.
Hi Alex, Thanks for youre great article! Very helpful.
I’ am trying to configure in the SCC environment a sensitivity label that give some restrictions for email (and its attachments) to external users. (as email to other companies), but I can’t figure out how to accomplish that. Is it possible that this configuration is not yet available in this platform? Is there an alternative?
Thanx in advance!
I think I need more detail about what you’re trying to accomplish and what issue you’re running into in order to answer that question.
Sorry that the question is unclear. What I like to accomplish is to create a custom label so that an end-user can secure an email message like the predefined ones, for example: (companyname)-confidential, of the (companyname)-view only.
With these two predefined ones it is not possible to email to external customers.
I was hoping that it is possible to create a custom label for example with the properties: view only and not allowed to print.
But for every label that I want to create I need to select users or groups from the tenant.
Hopefully I described the issue some more clearer and do you know the solution for it :-)
Thanx in advance!
Ah, yes! That is more clear. This can be done using the Azure admin center via Azure Info Protection, but in the Sensitivity labels area in 365 it is not easy: You could for instance put in a specific external domain (like a partner’s domain) and grant specific permissions per domain, but not specific external users. However, in AIP you can specify more granular, or specify user-defined permission for example. At least, that is how it is today.
Hi, Thanks for detailed info/ I have question . I have created label called private. when i send a mail with this option to user his inbox delegates also able to see this mail. which was not the case when i select private as a sensitivity under security settings. is that i make somthing with API itself or do i ask user to select both the option when they send private mails with in company.
How have you setup the label called private? In terms of email when a message is stamped with encryption and permissions, then only those recipients specified would be able to get the message, with Do Not Forward included then those recipients could not in turn re-share or forward the message on. However, note that if you have delegates they would be able to see the item in sent messages just fine, as there is no encryption applied on the sent item in that mailbox.
Hello Alex, thank you for all the explaination, details and screenshots. Today we are ending June/2019, do you know the last news about when these Sensitiviy labels are going to be applied in Office 365 Enterprise? it’s kinda confusing if it is gradually, still in progress or still “soon”. Thank you
Check out the roadmap–it says July CY2019. So yes, soon. https://www.microsoft.com/en-us/microsoft-365/roadmap?filters=&searchterms=sensitivity
I dont see the sesitivity labels that I created and published in my O365 business premium edition. Do I to do something else to see them?
Get a subscription that supports AIP plan 1, minimum.
Hey Alex,
Great article !!!
I have two questions on Retention labels:
1. Is there a way to notify a user that his document would be expiring on dd//yy and
2. Is there a way that the user can extend that retention period?
Yes, what you are referring to is called disposition review. See this article from Joanne Klein.
Great article @Alex.
It actually answered my many questions. However, I am left with below 5:
1. So we have a tool that is being used for document retention, does MS has any service may be like the AIP for example that could get the documents migrated to MS?
2. Is it possible to transfer the ownership of the documents from one to another owner? And the owners should be able to change the labels as well.
3. Do we have any admin reporting for the document with retention labels?
4. We are looking for a capability that should be capable of having a Hold Process ensuring that documents on hold must be preserved even if preservation exceeds the documents’ scheduled retention period, until the hold is released by the hold issuer
5. We want to know if this service would make a copy of each document that has a hold tag applied and automatically save it in a separate location where only the Hold Issuer (and delegates) maintains the copy of the original document and metadata including all modified versions until the hold is released
Please try to answer above
1. Not that I know of–my first guess is that you have to “unlabel” existing docs, then re-label with AIP. Check out ShareGate and Metalogix–they might have something? They have tools that help migrate files into SharePoint at least. Not sure about labels from some other vendor though…
2. Yes, you can set whatever co-ownership you want on a label, and change it anytime (the permission is defined at the label which lives in the cloud, the document gets stamped with a label, but it always has to check in with the service to see what that label “means”)
3. Yes, several options. Label activity explorer in Security & Compliance center, Audit log/MCAS, Content search/ eDiscovery
4. Litigation hold exists for Exchange Online but not SharePoint and OneDrive locations–I wouldn’t be surprised to see this change soon, as they have been working toward SEC 17a-4 (they have it with Exchange but not w/ SPO yet); nevertheless you could create a retention label (different than sensitivity label) and allow users to apply labels that outlast the defined retention policy (so if you had a policy for 3 years preservation plus deletion at the end, and a manually applied label for 5 years preservation–preservation always wins)
5. When a document is being preserved using a retention label/policy it goes into the preservation library in SPO, which is not a location you can “get to” but you can use Content search to pull that data as needed; the preservation library will contain the original doc and modifications as you mention. Somehow this is not considered compliant with 17a-4 (yet)–I don’t get it since it seems to be the same to me, but they are committed to making this happen and having official SEC 17a-4 compliance for SharePoint
Hey Alex,
I created some labels and deleted them because I was unable to edit the condition after creation.
My first question is: why are the values greyed out if a user wants to edit the condition after creation?
I had to delete that label and while re-creating it, I am getting error the Name already exists.
Second question: Where can i find this stale entry and delete it? so that i can use the same name again
Might be able to clear those stale entries out via PowerShell: https://docs.microsoft.com/en-us/azure/information-protection/rms-client/clientv2-admin-guide-customizations
Hey Alex. Thank you for your articles.
I have a question. Can I use Sensitivity labels in the coexistence of AD RMS and cloud services? If the organization moves from the local AD RMS to the cloud. At the moment, I can encrypt the document using the local AD RMS template and open it using the cloud AIP service. And vice versa – I can use the cloud-based AIP service to encrypt a document (but using a RMS template imported from the onPrem) and open this document on the onPrem using AD RMS.
Will similar coexistence work similarly when using sensetivity/unified labels?
That is only possible in AIP right now to my knowledge, but would love for someone to show me otherwise. :)
Hi Alex, great article. I have a question i hope you might answer. I have applied Sensitive labelling to my organisation, but we have offices in Germany where working with users personal data is against company policy and Works Council rules. We apply DLP to a sensitive label and this works fine. However within the Outlook Client when you compose an email and go to “Direct Replies To” you are able to enter different default sensitive labels. These are different to the sensitive ones I have currently created. Users seem to be using these labels too and this causes confussion. Is there any way to align these labels or to disable the ones used by the “Direct Replies To” option?
Ha! I had never even noticed that before. This is a good critique–similar to marking a message “Importance” you could also mark its “Sensitivity,” although I assume there was nothing other than a marking to it on the message, not any kind of enforcement as with the new Sensitivity labels. I doubt there is a way to turn that off, but MSFT would be smart to merge the labels into that selection, retiring the other markings, or just remove it entirely from this area.
I am heavy OWA user myself and I don’t know where you would go in OWA to find this same setting? Do you?
Hi Alex, OWA does not have the option to add different Sensitive Labels. However like the Outlook Client it does have its own Retention Policies as well. Not sure why Microsoft would allow you to create Retention Policies for Disposition when they have gone and created their own version of what they believe to be Retention Policies. Surely Retention Policies differ from Country to country and with GDPR Legislation this will surely not effect users in the US unless they are the Document Controllers and host European Data on their servers. Not sure why Microsoft is doing this as this is confusing engineers such as myself who are trying to implement AIP / DLP / Retention / AIP Scanner etc. The wonderful world of Microsoft.
Don’t know if I followed that 100% of the way through, but there are two main ways of publishing retention policies–right in EAC, and also using the Security & Compliance center. They recommend moving towards this new interface for configuring retention and deletion policies.
Thanks Alex for the above response.
Did you get a change to test the “Sites and group setting” for the label?
I have two questions:-
Can we and how:-
1. can we restrict the upload of the document to the same labeled site?(normal labeled doc to normal labeled site/Secret labeled doc to Secret labeled site) can you refer me to something so that I can test?
2. If above, cannot be done, then: can a SECRET labeled document SHOULD NOT be downloaded from a NORMAL labeled Sharepoint library to an untrusted device, but it SHOULD be allowed to be downloaded to a trusted device.
I have some newer articles on this topic, but I love the site and groups feature–it does not function as you describe, but you can see what options are available with that preview here. As well, I have an overview of the data protection options here–what you’re describing would probably be something you could do using MCAS with Conditional Access App Control policies–at least with regard to download (I don’t know if you can put rules around upload).
@alex
Thanks a ton!
You are great!!!
Great article!
I have a question about the behavior of expiration. If I have a Sensitivity label that causes documents/emails to expire after 7 days and I apply that Sensitivity label to an email, what exactly happens after 7 days? NO ONE can access it? Does it remain in the inbox/sent folder of the recipient/sender? Do I get an error when I try to open it?
Here’s the important question: What happens if either the sender or the recipient is put on litigation hold? Can an investigation still access that expired email? We are told that “a litigation hold trumps everything.” I wouldn’t think the message just deletes off the face of the earth after 7 days where even the admins can’t access it.
Thanks so much,
– Jeff J
Have not tested the specific scenario you describe–I don’t really use the expiration feature in production. However, there is a difference between the data owner and the persons with whom that data owner shares content. So when the owner labels a doc for example and sends a copy out to the recipient, let’s say it expires in 7 days. Recipient has 7 days to work with that doc before they can no longer open it–their access is no longer valid (the document doesn’t disappear, it’s just encrypted and their credentials are no longer good for it). I would expect then that the encrypted message remains indefinitely in the sent items folder of the individual who sent it, even if it expires for the recipients.
Thanks for responding so fast and thoroughly!
Hello Alex,
Read your post & wanted to create sensitive labels from S&C, but I have no option of Endpoint data loss prevention missing when creating Classification sensitivity label having an Microsoft Office 365 E5 license. Can u let me know how can I have this feature to be enabled
You would need Microsoft 365 E5, not Office 365 E5. Or, another subscription combo that includes both Intune and Azure Information Protection Plan 2. e.g. EM+S E5
Hello Alex,
I’ve noticed that labels with custom permissions [Let users assign permissions when they apply the label] are not showing in the Sensitivity column in SharePoint doclibs. Is this by design or did I do something wrong?
Tnx
Douglas
When you use the option to allow users to assign their own permissions, this is not compatible with the Online apps such as SharePoint, Word online, etc. You can use labels with static permissions only if you want them “readable” in the cloud. There are a bunch of “gotcha’s” to working with the labels in the cloud in fact. See: https://docs.microsoft.com/en-us/microsoft-365/compliance/sensitivity-labels-sharepoint-onedrive-files?view=o365-worldwide#limitations
Where are the labels for meeting invites? its just as sensitive as literally anything.
Example:
Meeting invite:
Subject: were selling our company
no tags …. OH NOOOOOOOOOOOOOOOOOOOOOOOOOOOO